STOP Djvu Ransomware Decryptor is a free decryptor created by Emsisoft and Michael Gillespie that allows everyone to decrypt files that were encrypted with the STOP ransomware. Currently, this decryptor can decrypt most variants of this ransomware (148 variants). Part of other versions of this ransomware, namely, cases when encrypted files have the extension: .DATAWAIT, .INFOWAIT, .puma, .pumax, .pumas, can be decrypted using STOP Puma decryptor. Unfortunately, in most cases, it is impossible to decrypt files that are encrypted with new versions of this ransomware (starting from August 2019). If you become a victim of one of these new variants, then at the moment you can only decrypt files that were encrypted with offline keys.
What is STOP Djvu Ransomware
STOP Djvu Ransomware is the most active and widespread ransomware. Like other ransomware, it is designed to encrypt files that can only be decrypted after payment of the ransom. According to the ID Ransomware, to date, more than 450,000 victims have already been discovered, and their number is increasing by approximately 1,500 people every day. The reason for this is that this ransomware is mainly distributed through adware, cracks, free programs and key generators, allowing users to activate paid software. Children, students and many other users, are looking for freeware, download and run it, not knowing that in this way they can allow the ransomware to penetrate on the computer.
Summary
| Name | STOP (Djvu) ransomware |
| Type | Crypto virus, Filecoder, Crypto malware, File locker, Ransomware |
| Encryption algorithm | The ransomware encrypts files using a strong encryption algorithm, which is called Salsa20. |
| Encrypted files extension | .STOP, .SUSPENDED, .WAITING, .PAUSA, .CONTACTUS, .DATASTOP, .STOPDATA, .KEYPASS, .WHY, .SAVEfiles, .DATAWAIT, .INFOWAIT, .puma, .pumax, .pumas, .shadow, .djvu, .djvuu, .udjvu, .djvuq, .uudjvu, .djvus, .djvur, .djvut .pdff, .tro, .tfude, .tfudeq, .tfudet, .rumba, .adobe, .adobee, .blower, .promos, .promoz, .promock, .promoks, .promorad, .promorad2, .kroput, .kroput1, .charck, .pulsar1, .klope, .kropun, .charcl, .doples, .luces, .luceq, .chech, .proden, .drume, .tronas, .trosak, .grovas, .grovat, .roland, .refols, .raldug, .etols, .guvara, .browec, .norvas, .moresa, .verasto, .hrosas, .kiratos, .todarius, .hofos, .roldat, .dutan, .sarut, .fedasot, .forasom, .berost, .fordan, .codnat, .codnat1, .bufas, .dotmap, .radman, .ferosas, .rectot, .skymap, .mogera, .rezuc, .stone, .redmat, .lanset, .davda, .poret, .pidon, .heroset, .myskle, .boston, .muslat, .gerosan, ,vesad, .horon, .neras, .truke, .dalle, .lotep, .nusar, .litar, .besub, .cezor, .lokas, .godes, .budak, .vusad, .herad, .berosuce, .gehad, .gusau, .madek, .tocue, .darus, .lapoi, .todar, .dodoc, .bopador, .novasof, .ntuseg, .ndarod, .access, .format, .nelasod, .mogranos, .cosakos, .nvetud, .lotej, .kovasoh, prandel, .zatrov, .masok, .brusaf, londec, .krusop, .mtogas, .coharos, .nasoh, .nacro, .pedro, .nuksus, .vesrato, .masodas, .stare, .cetori, .carote, .shariz, .gero, .hese, .geno, .xoza, .seto, .peta, .moka, .meds, .kvag, .domn, .karl, .nesa, .boot, .noos, .kuub, .reco, .bora, .leto, nols, werd, .coot, .derp, .nakw, .meka, .toec, .mosk, .lokf, .peet, .grod, .mbed, .kodg, .zobm, .rote, .msop, .hets, .righ, .gesd, .merl, .nbes, .mkos, .piny, .redl, .kodc, .nosu, .reha, .topi, .npsg, .btos, .repp, .alka, .bboo, rooe, .mmnn, .ooss, .mool, .nppp, .rezm, .lokd, .foop, .remk, .npsk, opqz, .mado, jope, .mpaj, .lalo, .lezp, .qewe, .mpal, .sqpc, .mzlq, .koti, .covm, .pezi, .nlah, .kkll, .zwer, .nypd, .usam, .tabe, .vawe, .moba, .pykw, .zida, .maas, .repl, .kuus, .erif, .kook, .nile, .oonn, .vari, .boop, .kasp, .ogdo, .npph, .kolz, .copa, .lyli, .moss, .foqe, .mmpa, .efji, .iiss, .jdyi, .vpsh, .agho, .vvoa, .epor, .sglh, .lisp, .weui, .nobu, .igdm, .booa, .omfl, igal, .qlkm, .coos, .wbxd, .pola, .cosd, .plam, .ygkz, .cadq, .ribd, .tirp, .reig, .enfp, .ekvf, .ytbn, .fdcz, .urnb, .lmas, .wrui, .rejg, .pcqq, .igvm, .nusm, .ehiz, .paas, .pahd, .mppq, .qscx, .sspq, .iqll, .ddsg, .piiq, .miis, .neer, .leex, .zqqw, .pooe, .lssr, .zzla, .wwka, .gujd, .ufwj, .moqs, .aeur, .guer, .nooa, .reqg, .hoop, .orkf, .lqqw, .efdc, .wiot, .koom, .rigd, .tisc, .nqsq, .irjg, .vtua, .maql, .zaps, .rugj, .cool, .palq, .stax, .irfk, .qdla, .futm, .utjg, .iisa, .pqgs, .rigj, .robm, .moia, .wnlu, .hgsh, .nnqp, .miia, .loov, .dehd, .nqhd, .vfgj, .maak, .qqqw, .yoqs, .avyu, .cuag, .iips, .qnty, .ccps, .ckae, .eucy, .ooii, .rtgf, .fgui, .fgnh, .iiof, .vyia, .vtym, .kqgs, .bpqd, .rguy, .kkia, .mmuz, .wdlo, .kxde, .udla, .mpag, .gtys, .tuid, .uyjh, .msjd, .jhdd, .dmay, .jhbg, .dewd, .sijr, .bbnm, .byya, .ifla, .errz, .dfwe, .fdcv, .nnuz, .qlln, .rrbb, .rryy, .bbyy, .bbii, .bbzz, .hkgt, .efvc, .lltt, .lloo, .llee, .dkrf, .eiur, .ghsd, .jjll, .hhew, .hhwq, .ggew, .ggeo, .ggwq, .ggyu, .ooxa, .oori, .vvew, .vvyu, .vvwq, .vveo, .vvyu, .qqmt, .cdmx , .cdqw |
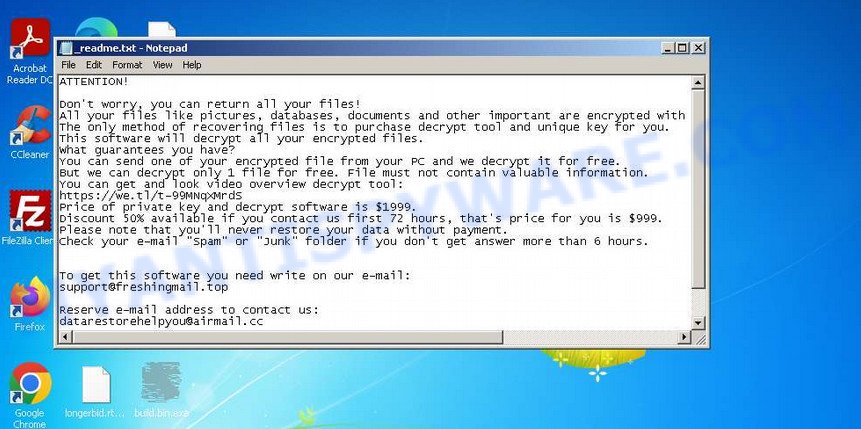
| Ransom note | In each directory where the ransomware encrypted the files, it drops a new file (ransom demand message). The very first versions of STOP used the following file names: !!!YourDataRestore!!!.txt, !!!RestoreProcess!!!.txt, !!!INFO_RESTORE!!!.txt, !!RESTORE!!!.txt, !!!!RESTORE_FILES!!!.txt, !!!DATA_RESTORE!!!.txt, !!!RESTORE_DATA!!!.txt, !!!KEYPASS_DECRYPTION_INFO!!!.txt, !!!WHY_MY_FILES_NOT_OPEN!!!.txt, !!!SAVE_FILES_INFO!!!.txt and !readme.txt. Starting with the version that, after encryption, added the .djvu * extension, the ransom note had the following file name: _openme.txt, _open_.txt or _readme.txt. The most recent versions of the STOP Djvu Ransomware use only one file name: _readme.txt. |
| Contacts | STOP ransomware developers often change the email addresses that are used to contact victims, the last of them are listed below: support@freshingmail.top, datarestorehelp@airmail.cc, support@bestyourmail.ch, admin@helpdata.top, manager@time2mail.ch, supportsys@airmail.cc, support@sysmail.ch, helprestoremanager@airmail.cc, manager@mailtemp.ch, supporthelp@airmail.cc, helpteam@mail.ch, restoremanager@airmail.cc, restoreadmin@firemail.cc, restoremanager@firemail.cc, helpdatarestore@firemail.cc, helpmanager@mail.ch, helpmanager@firemail.cc , helpmanager@iran.ir, helprestore@firemail.cc, datarestore@iran.ir, datarestorehelp@firemail.cc, datahelp@iran.ir, restorealldata@firemail.cc, restorefiles@firemail.cc, restoredatahelp@firemail.cc, salesrestoresoftware@firemail.cc, salesrestoresoftware@gmail.com, gorentos@bitmessage.ch |
| Ransom amount | $1999, $999 (if paid within 72 hours) |
| Encryption keys | Security researchers have determined that STOP Djvu Ransomware uses two types of encryption keys. The first one is online keys, the ransomware uses these keys if during encryption it has access to the network and can connect to its command-and-control server. These keys are unique to each computer. The second group is offline keys. The ransomware uses these keys if it does not have a connection to its command-and-control server. These keys are the same for different computers. That is, the same key can be used to decrypt files regardless of which computer they were encrypted on. To date, security researchers have found offline keys for some variants of STOP Djvu Ransomware. |
How to decrypt files encrypted by STOP Djvu Ransomware
Depending on the version of STOP Djvu Ransomware, you need to perform different steps to decrypt files. The version of STOP Djvu can be determined by the extension of the encrypted files. Before decrypting files, you need to be 100% sure that the ransomware is completely removed. We recommend that you use several tools (with different anti-virus engines) to scan your computer and remove STOP Ransomware and other malware. Some of the best and free malware removal tools are listed in this article – Best Free Malware Removal Tools.
1. Old STOP ransomware
A variant of STOP ransomware using the extension: .puma, .pumas, .pumax. All known variants of this ransomware can be decrypted using STOP Puma decryptor. Also, with this decryptor, in some cases, files with the following extension can be decrypted: .STOP, .SUSPENDED, .WAITING, .PAUSA, .CONTACTUS, .DATASTOP, .STOPDATA, .KEYPASS, .WHY, .SAVEfiles, .DATAWAIT, .INFOWAIT.
Download the decryptor from the link below
https://www.emsisoft.com/ransomware-decryption-tools/stop-puma
Right-click on the downloaded file (decrypt_STOPPuma.exe) and select “Run as Administartor”. You will be shown the license terms, click yes to continue. The program starts, you will see a window, as in the example below.
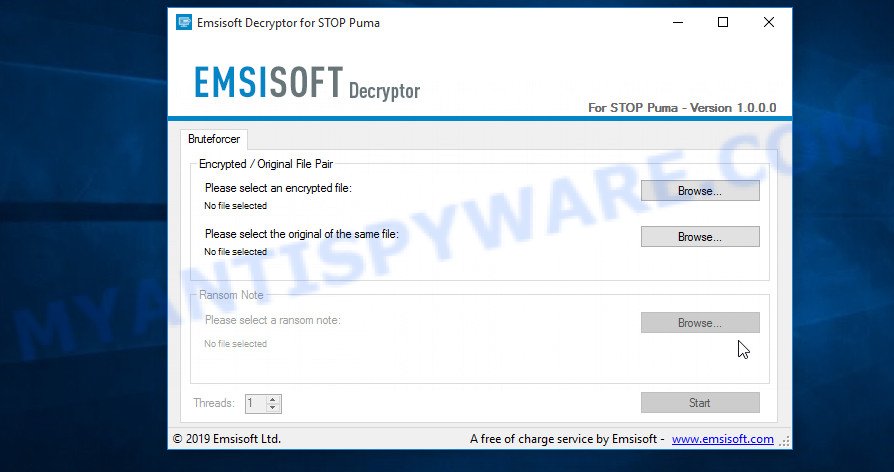
STOP Puma decryptor
As we already reported above, in order to use this decryptor you need one, or better, several pairs of files, one of which is encrypted, and the other is its original version. Having prepared the corresponding pairs, then you need to select them using the corresponding buttons in the program window. When ready, press the Start button. As soon as the key is found, the decryptor will immediately inform you. In some cases, an error may occur while searching for a key, therefore we recommend using several pairs of files to be sure that the correct key has been found.
After the correct key is found, you will be able to decrypt the files. Select the location where the encrypted files are located and click the Decrypt button.
2. STOP Djvu ransomware
A variant of the STOP Djvu ransomware using the extension: .shadow, .djvu, .djvur, .djvuu, .udjvu, .uudjvu, .djvuq, .djvus, .djvur, .djvut, .pdff, .tro, .tfude, .tfudet, .tfudeq, .rumba, .adobe, .adobee, .blower, .promos, .promoz, .promorad, .promock, .promok, .promorad2, .kroput, .kroput1, .pulsar1, .kropun1, .charck, .klope, .kropun, .charcl, .doples, .luces, .luceq, .chech, .proden, .drume, .tronas, .trosak, .grovas, .grovat, .roland, .refols, .raldug, .etols, .guvara, .browec, .norvas, .moresa, .vorasto, .hrosas, .kiratos, .todarius, .hofos, .roldat, .dutan, .sarut, .fedasot, .berost, .forasom, .fordan, .codnat, .codnat1, .bufas, .dotmap, .radman, .ferosas, .rectot, .skymap, .mogera, .rezuc, .stone, .redmat, .lanset, .davda, .poret, .pidom, .pidon, .heroset, .boston, .muslat, .gerosan, .vesad, .horon, .neras, .truke, .dalle, .lotep, .nusar, .litar, .besub, .cezor, .lokas, .godes, .budak, .vusad, .herad, .berosuce, .gehad, .gusau, .madek, .darus, .tocue, .lapoi, .todar, .dodoc, .bopador, .novasof, .ntuseg, .ndarod, .access, .format, .nelasod, .mogranos, .cosakos, .nvetud, .lotej, .kovasoh, .prandel, .zatrov, .masok, .brusaf, .londec, .krusop, .mtogas, .nasoh, .nacro, .pedro, .nuksus, .vesrato, .masodas, .cetori, .stare, .carote.
In order to decrypt files you need to find several pairs of files. Each pair of files consists of an encrypted file and its original copy. File size over 150kb. After you find several pairs of files, do the following. Open the following link in a new window.
https://decrypter.emsisoft.com/submit/stopdjvu/
You will see a page called STOP Djvu Decryption. An example of this page is given below.
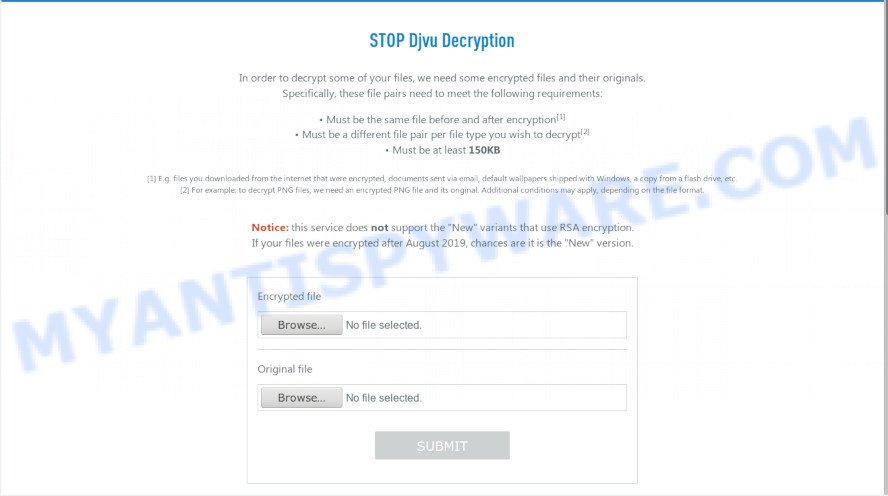
STOP Djvu Decryption
On this page using the Browse button, enter the path to the encrypted file and its original copy, then click the Submit button. After clicking on the Submit button, your files will be uploaded to the server. Then the key search process starts. Please be patient, this process may take some time. As soon as the key is found, an appropriate message will appear on the page and you will be asked to download the decryptor.
Click on the link called “Click here to download the decryptor“. The page from which you can download the decryptor will load. Click the Download button and save the decrypt_STOPDjvu.exe file to your computer.
When the file is downloaded, start it by right-clicking on it and selecting item “Run as Administrator”. When it starts, the Windows can show you UAC Promt, then click Yes. After that, you will be shown the license terms and a small instruction, please read this information to continue.
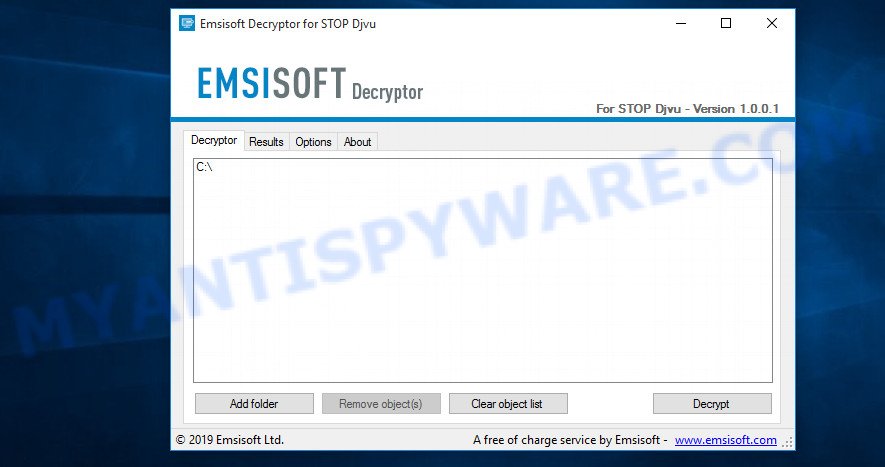
STOP Djvu decryptor
In the main window, select the disk or directory where the encrypted files are located, and then click Decrypt. After that, the decryptor will begin to decrypt the files for which the key was found at the previous stage. If the decryptor skips files, saying that it cannot decrypt them, then you need to again find a couple of files, one of which is encrypted, and the second is its original copy. Then use them to find the decryption key.
3. New Djvu ransomware
The latest version of STOP Djvu ransomware uses the following file extensions: .coharos, .shariz, .gero, .hese, .geno, .xoza, .seto, peta, .moka, .meds, .kvag, .domn, .karl, .nesa, .boot, .kuub, .reco, .bora, .leto, nols, werd, .coot, .derp, .nakw, .meka, .toec, .mosk, .lokf, .peet, grod, .mbed, .kodg, .zobm, .rote, .msop, .hets, .righ, .gesd, .merl, .nbes, .mkos, .piny, .redl, kodc, .nosu, .reha, .topi, .npsg, .btos, .repp, .alka, .bboo, rooe, .mmnn, .ooss, .mool, .nppp, .rezm, .lokd, .foop, .remk, .npsk, opqz, .mado, jope, .mpaj, .lalo, .lezp, .qewe, .mpal, .sqpc, .mzlq, .koti, .covm, .pezi, .nlah, .kkll, .zwer, .nypd, .usam, .tabe, .vawe, .moba, .pykw, .zida, .maas, .repl, .kuus, .erif, .kook, .nile, .oonn, .vari, .boop, .kasp, .ogdo, .npph, .kolz, .copa, .lyli, .moss, .foqe, .mmpa, .efji, .iiss, .jdyi, .vpsh, .agho, .vvoa, .epor, .sglh, .lisp, .weui, .nobu, .igdm, .booa, .omfl, igal, .qlkm, .coos, .wbxd, .pola, .cosd, .plam, .ygkz, .cadq, .ribd, .tirp, .reig, .enfp, .ekvf, .ytbn, .fdcz, .urnb, .lmas, .wrui, .rejg, .pcqq, .igvm, .nusm, .ehiz, .paas, .pahd, .mppq, .qscx, .sspq, .iqll, .ddsg, .piiq, .miis, .neer, .leex, .zqqw, .pooe, .lssr, .zzla, .wwka, .gujd, .ufwj, .moqs, .aeur, .guer, .nooa, .reqg, .hoop, .orkf, .lqqw, .efdc, .wiot, .koom, .rigd, .tisc, .nqsq, .irjg, .vtua, .maql, .zaps, .rugj, .cool, .palq, .stax, .irfk, .qdla, .futm, .utjg, .iisa, .pqgs, .rigj, .robm, .moia, .wnlu, .hgsh, .nnqp, .miia, .loov, .dehd, .nqhd, .vfgj, .maak, .qqqw, .yoqs, .avyu, .cuag, .iips, .qnty, .ccps, .ckae, gcyi, .eucy, .ooii, .rtgf, .fgui, .fgnh, .iiof, .vyia, .vtym, .kqgs, .bpqd, .rguy, .kkia, .mmuz, .wdlo, .kxde, .udla, .mpag, .gtys, .tuid, .uyjh, .msjd, .jhdd, .dmay, .jhbg, .dewd, .sijr, .bbnm, .byya, .ifla, .errz, .dfwe, .fdcv, .nnuz, .qlln, .rrbb, .rryy, .bbyy, .bbii, .bbzz, .hkgt, .efvc, .lltt, .lloo, .llee, .dkrf, .eiur, .ghsd, .jjll, .hhew, .hhwq, .ggew, .ggeo, .ggwq, .ggyu, .ooxa, .oori, .vvew, .vvyu, .vvwq, .vveo, .vvyu, .qqmt. An updated variant of this version appears every few days, the main difference between all variants is the extension of encrypted files. The last variant encrypts files with the .qqmt extension; the personal ID of the victims of this variant starts with 0540.
At the moment, it is possible to decrypt files only in some cases when they are encrypted using an offline key. To decrypt files, download the decryptor using the following link.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Click the Download button and save the decrypt_STOPDjvu.exe file to your computer. Right click to it and select ‘Run as Administrator’. Confirm permission to run the program by pressing the Yes button. Read the license terms and brief instructions. In the main window that opens, select the disk or folder where the encrypted files are located and click the Decrypt button. If the decryptor skips files without decrypting them, then the offline key for them is unknown or they are encrypted with an online key.
This video step-by-step guide will demonstrate How to decrypt files locked by STOP Djvu ransomware.
Finish words
We hope that the set of utilities and services developed by Emsisoft and Michael Gillespie helped you decrypt all the files. If the decryption of the files failed, then do not forget that there is another way to recover your files – is to use data recovery tools. Details on how to recover encrypted files without a key and decryptor are described in the article:
How To Recover Encrypted Files (Ransomware file recovery).


















File: Data ukuran seragam tx daerahAceh.xls.mbed
Unable to decrypt Old Variant ID: wjN4KGaI6SxMMUTI2T3R3vP4NuAHnTQxQzp8Wwar
First 5 bytes: D0CF11E0A1
Unable to decrypt Old Variant ID: 7757TLxCRXnSjhJoq4TruFpvTlag0OKn6hPITYt1 as you can see its t1 code. but this is the msg your decrypter is showing for every file. can you help?
0175Asd374y5iuhldNXAl7xFWihf8Gn6Bg3i1JsBd7yvrty3UhGsDCLCY0184Asd374y5wjN4KGaI6SxMMUTI2T3R3vP4NuAHnTQxQzp8Wwar
wjN4KGaI6SxMMUTI2T3R3vP4NuAHnTQxQzp8Wwar
These IDs are related to online keys, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
Jack, your ID ends in ‘t1’, which means that your files are encrypted offline key and they can be decrypted. The fact that the decryptor skips them and does not decrypt them shows that security researchers have not yet determined the decryption key, so you just need to wait. Just try to decrypt your files from time to time.
Is there a possibility in future that .reha file can be decrypted if they are encrypted online?
0202a7d6a8sdaoMJV9PzMpdS5VNGorDryzKfSrfsHHFckazmEUlfY
Shivam, if your files are encrypted with an online key, then their decryption is impossible since there is no way to find out the decryption key. Try to restore the contents of encrypted files using the following guide: How to recover encrypted files.
The “0202a7d6a8sdaoMJV9PzMpdS5VNGorDryzKfSrfsHHFckazmEUlfY” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
please help
0205a7d6a8sdauvEETK84RPC0Q5icp67CP746LJaCJuwq2tG9Kjt1
bboo
Your personal ID:
0205a7d6a8sdasMNVqkJoFGx3pIQfXpZPRjBR1Hg6Ry2znGLHU27I
system ID
sMNVqkJoFGx3pIQfXpZPRjBR1Hg6Ry2znGLHU27I
Your personal ID:
0205a7d6a8sdaO0k9ApJHPx9R2J4JqPYnYFphuut0vJTnVed6uRML
Personal ID
O0k9ApJHPx9R2J4JqPYnYFphuut0vJTnVed6uRML
Sir,Please help me.I have very important data.
yhunnus, the ‘0205a7d6a8sdauvEETK84RPC0Q5icp67CP746LJaCJuwq2tG9Kjt1’ id means that your files are encrypted with an offline key, but security researchers have not yet determined this key. Therefore, you need to wait from time to time trying to decrypt .bboo files.
sMNVqkJoFGx3pIQfXpZPRjBR1Hg6Ry2znGLHU27I
0205a7d6a8sdaO0k9ApJHPx9R2J4JqPYnYFphuut0vJTnVed6uRML
These ID’s are related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
Unable to decrypt file with ID:
0210a7d6rNv0MzMDj9HnSG1V89IQXFQSktYSTyIGTje3fXK1
The “0210a7d6rNv0MzMDj9HnSG1V89IQXFQSktYSTyIGTje3fXK1” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
NPPP Virus
all my files chenged to NPPP
Your personal ID:
0210a7d6ggsVKGJk2lzUYTNacFjobLLB7nCW7YUL9W5isNJY
what can I do?
Please help
The “0210a7d6ggsVKGJk2lzUYTNacFjobLLB7nCW7YUL9W5isNJY” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
Hi,
is it possible to decrypt the file .merl ?
What can I do, please help ?
Currently, you cannot decrypt .merl files encrypted with an online key, and .merl files encrypted with an offline key (security researchers have not yet determined the offline key). Therefore, the only chance to restore the contents of encrypted files is to use data recovery utilities. This is described in detail in the following article:
How to recover ransomware encrypted files.
Thank you!
I will try.
Your personal ID:
0213Asd4a7d6y6X6R0SS0v2mAGJpKjpOtWa4iJXw8heCox15Rluf
All my files changed to foop
How can i save this poisonous situation?
Please help
The “0213Asd4a7d6y6X6R0SS0v2mAGJpKjpOtWa4iJXw8heCox15Rluf” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
Dear admin ,
Pls help. I have just been infected & all my files are excrypted with “.lokd”, yesterday 13th March 2020.
Thank you
Contributing to the info list “To be decrypted” in the future:
No key for New Variant offline ID: ZHwhSWv4UBPdta8bPx4MWySjbd1cTioHb6WL3Bt1
Notice: this ID appears be an offline ID, decryption MAY be possible in the future
Your personal ID:
0212Asd4a7d6ZHwhSWv4UBPdta8bPx4MWySjbd1cTioHb6WL3Bt1
Unfortunately, the security researchers have not yet determined the offline key, so at the moment you can’t decrypt .lokd files. But decryption is likely to be available in the future. I advise you to copy all the important encrypted files to a separate disk, copy files _readme.txt and PERSONALID.txt to the same place. After that, be patient and wait for the offline key to be found.
Is there any encryptor available for .remk files?
If the .remk files are encrypted with an offline key, then they can be decrypted in the future, since researchers have not yet determined the offline key. In any case, you can try to restore the contents of encrypted files using the following instructions:
How to recover ransomware encrypted files.
does not work.
id:0203asdoeoOOdf2PH4JEEYVDxRJkvHC0GcNs9DlHAqy5ZiHxh1IYCx
The “0203asdoeoOOdf2PH4JEEYVDxRJkvHC0GcNs9DlHAqy5ZiHxh1IYCx” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
Please help!!
To get this software you need write on our e-mail:
helpdatarestore@firemail.cc
Reserve e-mail address to contact us:
helpmanager@mail.ch
Your personal ID:
0214OIQuhkjdA7uvPCYwP5lS8BjqU0WAODuNFnfDIse2c2V4obnE
.remk
The “0214OIQuhkjdA7uvPCYwP5lS8BjqU0WAODuNFnfDIse2c2V4obnE” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
Dear admin ,
Pls help. I have just been infected & all my files are excrypted with “.npsk”, on 22th March 2020.
Is decryption MAY be possible in the future
Your personal ID:
0215Asd4a7d6cNH5YagcalZDILbCDNvsse3q0rnnMyuYME2ZLm6C
The “0215Asd4a7d6cNH5YagcalZDILbCDNvsse3q0rnnMyuYME2ZLm6C” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
To get this software you need write on our e-mail:
helpdatarestore@firemail.cc
Reserve e-mail address to contact us:
helpmanager@mail.ch
Your personal ID:
0216OIWojlj48UkZBfOdM3F7elvftiQaHkxkLxIyfLstL8IurjdP5
STOP Djvu
can i have decrypter tool?
Identified by:
ransomnote_email: helpmanager@mail.ch
sample_extension: .opqz
sample_bytes: [0xABD7 – 0xABFD] 0x7B33364136393842392D443637432D344530372D424538322D3045433542313442344446357D
waiting for your response!
The “0216OIWojlj48UkZBfOdM3F7elvftiQaHkxkLxIyfLstL8IurjdP5” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Please help
No key for New Variant online ID: D6bfV9UbyWlP65lQohY0AMYCuJgJ3AbKsz8x6eWK
Notice: this ID appears to be an online ID, decryption is impossible
The “D6bfV9UbyWlP65lQohY0AMYCuJgJ3AbKsz8x6eWK” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Todos mis archivos estan con el virus opqz
como le puedo hacer. ayuda ayuda plis
Use the following steps:
https://www.myantispyware.com/2020/03/26/how-to-remove-opqz-ransomware-virus-decrypt-opqz-files/