STOP Djvu Ransomware Decryptor is a free decryptor created by Emsisoft and Michael Gillespie that allows everyone to decrypt files that were encrypted with the STOP ransomware. Currently, this decryptor can decrypt most variants of this ransomware (148 variants). Part of other versions of this ransomware, namely, cases when encrypted files have the extension: .DATAWAIT, .INFOWAIT, .puma, .pumax, .pumas, can be decrypted using STOP Puma decryptor. Unfortunately, in most cases, it is impossible to decrypt files that are encrypted with new versions of this ransomware (starting from August 2019). If you become a victim of one of these new variants, then at the moment you can only decrypt files that were encrypted with offline keys.
What is STOP Djvu Ransomware
STOP Djvu Ransomware is the most active and widespread ransomware. Like other ransomware, it is designed to encrypt files that can only be decrypted after payment of the ransom. According to the ID Ransomware, to date, more than 450,000 victims have already been discovered, and their number is increasing by approximately 1,500 people every day. The reason for this is that this ransomware is mainly distributed through adware, cracks, free programs and key generators, allowing users to activate paid software. Children, students and many other users, are looking for freeware, download and run it, not knowing that in this way they can allow the ransomware to penetrate on the computer.
Summary
| Name | STOP (Djvu) ransomware |
| Type | Crypto virus, Filecoder, Crypto malware, File locker, Ransomware |
| Encryption algorithm | The ransomware encrypts files using a strong encryption algorithm, which is called Salsa20. |
| Encrypted files extension | .STOP, .SUSPENDED, .WAITING, .PAUSA, .CONTACTUS, .DATASTOP, .STOPDATA, .KEYPASS, .WHY, .SAVEfiles, .DATAWAIT, .INFOWAIT, .puma, .pumax, .pumas, .shadow, .djvu, .djvuu, .udjvu, .djvuq, .uudjvu, .djvus, .djvur, .djvut .pdff, .tro, .tfude, .tfudeq, .tfudet, .rumba, .adobe, .adobee, .blower, .promos, .promoz, .promock, .promoks, .promorad, .promorad2, .kroput, .kroput1, .charck, .pulsar1, .klope, .kropun, .charcl, .doples, .luces, .luceq, .chech, .proden, .drume, .tronas, .trosak, .grovas, .grovat, .roland, .refols, .raldug, .etols, .guvara, .browec, .norvas, .moresa, .verasto, .hrosas, .kiratos, .todarius, .hofos, .roldat, .dutan, .sarut, .fedasot, .forasom, .berost, .fordan, .codnat, .codnat1, .bufas, .dotmap, .radman, .ferosas, .rectot, .skymap, .mogera, .rezuc, .stone, .redmat, .lanset, .davda, .poret, .pidon, .heroset, .myskle, .boston, .muslat, .gerosan, ,vesad, .horon, .neras, .truke, .dalle, .lotep, .nusar, .litar, .besub, .cezor, .lokas, .godes, .budak, .vusad, .herad, .berosuce, .gehad, .gusau, .madek, .tocue, .darus, .lapoi, .todar, .dodoc, .bopador, .novasof, .ntuseg, .ndarod, .access, .format, .nelasod, .mogranos, .cosakos, .nvetud, .lotej, .kovasoh, prandel, .zatrov, .masok, .brusaf, londec, .krusop, .mtogas, .coharos, .nasoh, .nacro, .pedro, .nuksus, .vesrato, .masodas, .stare, .cetori, .carote, .shariz, .gero, .hese, .geno, .xoza, .seto, .peta, .moka, .meds, .kvag, .domn, .karl, .nesa, .boot, .noos, .kuub, .reco, .bora, .leto, nols, werd, .coot, .derp, .nakw, .meka, .toec, .mosk, .lokf, .peet, .grod, .mbed, .kodg, .zobm, .rote, .msop, .hets, .righ, .gesd, .merl, .nbes, .mkos, .piny, .redl, .kodc, .nosu, .reha, .topi, .npsg, .btos, .repp, .alka, .bboo, rooe, .mmnn, .ooss, .mool, .nppp, .rezm, .lokd, .foop, .remk, .npsk, opqz, .mado, jope, .mpaj, .lalo, .lezp, .qewe, .mpal, .sqpc, .mzlq, .koti, .covm, .pezi, .nlah, .kkll, .zwer, .nypd, .usam, .tabe, .vawe, .moba, .pykw, .zida, .maas, .repl, .kuus, .erif, .kook, .nile, .oonn, .vari, .boop, .kasp, .ogdo, .npph, .kolz, .copa, .lyli, .moss, .foqe, .mmpa, .efji, .iiss, .jdyi, .vpsh, .agho, .vvoa, .epor, .sglh, .lisp, .weui, .nobu, .igdm, .booa, .omfl, igal, .qlkm, .coos, .wbxd, .pola, .cosd, .plam, .ygkz, .cadq, .ribd, .tirp, .reig, .enfp, .ekvf, .ytbn, .fdcz, .urnb, .lmas, .wrui, .rejg, .pcqq, .igvm, .nusm, .ehiz, .paas, .pahd, .mppq, .qscx, .sspq, .iqll, .ddsg, .piiq, .miis, .neer, .leex, .zqqw, .pooe, .lssr, .zzla, .wwka, .gujd, .ufwj, .moqs, .aeur, .guer, .nooa, .reqg, .hoop, .orkf, .lqqw, .efdc, .wiot, .koom, .rigd, .tisc, .nqsq, .irjg, .vtua, .maql, .zaps, .rugj, .cool, .palq, .stax, .irfk, .qdla, .futm, .utjg, .iisa, .pqgs, .rigj, .robm, .moia, .wnlu, .hgsh, .nnqp, .miia, .loov, .dehd, .nqhd, .vfgj, .maak, .qqqw, .yoqs, .avyu, .cuag, .iips, .qnty, .ccps, .ckae, .eucy, .ooii, .rtgf, .fgui, .fgnh, .iiof, .vyia, .vtym, .kqgs, .bpqd, .rguy, .kkia, .mmuz, .wdlo, .kxde, .udla, .mpag, .gtys, .tuid, .uyjh, .msjd, .jhdd, .dmay, .jhbg, .dewd, .sijr, .bbnm, .byya, .ifla, .errz, .dfwe, .fdcv, .nnuz, .qlln, .rrbb, .rryy, .bbyy, .bbii, .bbzz, .hkgt, .efvc, .lltt, .lloo, .llee, .dkrf, .eiur, .ghsd, .jjll, .hhew, .hhwq, .ggew, .ggeo, .ggwq, .ggyu, .ooxa, .oori, .vvew, .vvyu, .vvwq, .vveo, .vvyu, .qqmt, .cdmx , .cdqw |
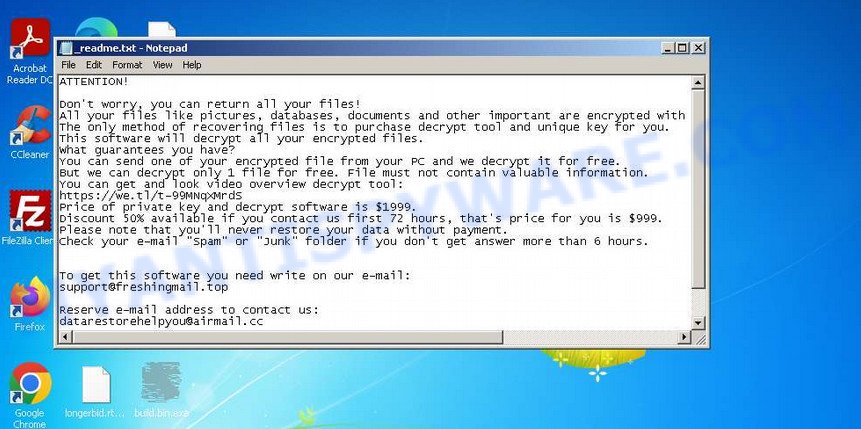
| Ransom note | In each directory where the ransomware encrypted the files, it drops a new file (ransom demand message). The very first versions of STOP used the following file names: !!!YourDataRestore!!!.txt, !!!RestoreProcess!!!.txt, !!!INFO_RESTORE!!!.txt, !!RESTORE!!!.txt, !!!!RESTORE_FILES!!!.txt, !!!DATA_RESTORE!!!.txt, !!!RESTORE_DATA!!!.txt, !!!KEYPASS_DECRYPTION_INFO!!!.txt, !!!WHY_MY_FILES_NOT_OPEN!!!.txt, !!!SAVE_FILES_INFO!!!.txt and !readme.txt. Starting with the version that, after encryption, added the .djvu * extension, the ransom note had the following file name: _openme.txt, _open_.txt or _readme.txt. The most recent versions of the STOP Djvu Ransomware use only one file name: _readme.txt. |
| Contacts | STOP ransomware developers often change the email addresses that are used to contact victims, the last of them are listed below: support@freshingmail.top, datarestorehelp@airmail.cc, support@bestyourmail.ch, admin@helpdata.top, manager@time2mail.ch, supportsys@airmail.cc, support@sysmail.ch, helprestoremanager@airmail.cc, manager@mailtemp.ch, supporthelp@airmail.cc, helpteam@mail.ch, restoremanager@airmail.cc, restoreadmin@firemail.cc, restoremanager@firemail.cc, helpdatarestore@firemail.cc, helpmanager@mail.ch, helpmanager@firemail.cc , helpmanager@iran.ir, helprestore@firemail.cc, datarestore@iran.ir, datarestorehelp@firemail.cc, datahelp@iran.ir, restorealldata@firemail.cc, restorefiles@firemail.cc, restoredatahelp@firemail.cc, salesrestoresoftware@firemail.cc, salesrestoresoftware@gmail.com, gorentos@bitmessage.ch |
| Ransom amount | $1999, $999 (if paid within 72 hours) |
| Encryption keys | Security researchers have determined that STOP Djvu Ransomware uses two types of encryption keys. The first one is online keys, the ransomware uses these keys if during encryption it has access to the network and can connect to its command-and-control server. These keys are unique to each computer. The second group is offline keys. The ransomware uses these keys if it does not have a connection to its command-and-control server. These keys are the same for different computers. That is, the same key can be used to decrypt files regardless of which computer they were encrypted on. To date, security researchers have found offline keys for some variants of STOP Djvu Ransomware. |
How to decrypt files encrypted by STOP Djvu Ransomware
Depending on the version of STOP Djvu Ransomware, you need to perform different steps to decrypt files. The version of STOP Djvu can be determined by the extension of the encrypted files. Before decrypting files, you need to be 100% sure that the ransomware is completely removed. We recommend that you use several tools (with different anti-virus engines) to scan your computer and remove STOP Ransomware and other malware. Some of the best and free malware removal tools are listed in this article – Best Free Malware Removal Tools.
1. Old STOP ransomware
A variant of STOP ransomware using the extension: .puma, .pumas, .pumax. All known variants of this ransomware can be decrypted using STOP Puma decryptor. Also, with this decryptor, in some cases, files with the following extension can be decrypted: .STOP, .SUSPENDED, .WAITING, .PAUSA, .CONTACTUS, .DATASTOP, .STOPDATA, .KEYPASS, .WHY, .SAVEfiles, .DATAWAIT, .INFOWAIT.
Download the decryptor from the link below
https://www.emsisoft.com/ransomware-decryption-tools/stop-puma
Right-click on the downloaded file (decrypt_STOPPuma.exe) and select “Run as Administartor”. You will be shown the license terms, click yes to continue. The program starts, you will see a window, as in the example below.
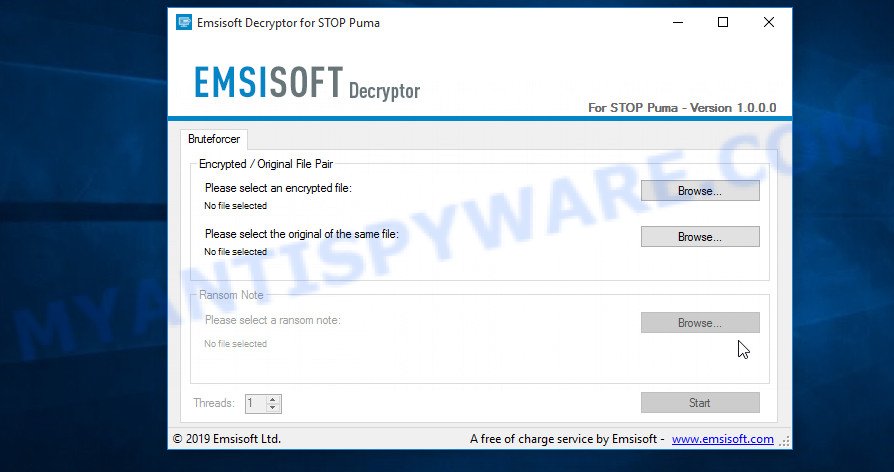
STOP Puma decryptor
As we already reported above, in order to use this decryptor you need one, or better, several pairs of files, one of which is encrypted, and the other is its original version. Having prepared the corresponding pairs, then you need to select them using the corresponding buttons in the program window. When ready, press the Start button. As soon as the key is found, the decryptor will immediately inform you. In some cases, an error may occur while searching for a key, therefore we recommend using several pairs of files to be sure that the correct key has been found.
After the correct key is found, you will be able to decrypt the files. Select the location where the encrypted files are located and click the Decrypt button.
2. STOP Djvu ransomware
A variant of the STOP Djvu ransomware using the extension: .shadow, .djvu, .djvur, .djvuu, .udjvu, .uudjvu, .djvuq, .djvus, .djvur, .djvut, .pdff, .tro, .tfude, .tfudet, .tfudeq, .rumba, .adobe, .adobee, .blower, .promos, .promoz, .promorad, .promock, .promok, .promorad2, .kroput, .kroput1, .pulsar1, .kropun1, .charck, .klope, .kropun, .charcl, .doples, .luces, .luceq, .chech, .proden, .drume, .tronas, .trosak, .grovas, .grovat, .roland, .refols, .raldug, .etols, .guvara, .browec, .norvas, .moresa, .vorasto, .hrosas, .kiratos, .todarius, .hofos, .roldat, .dutan, .sarut, .fedasot, .berost, .forasom, .fordan, .codnat, .codnat1, .bufas, .dotmap, .radman, .ferosas, .rectot, .skymap, .mogera, .rezuc, .stone, .redmat, .lanset, .davda, .poret, .pidom, .pidon, .heroset, .boston, .muslat, .gerosan, .vesad, .horon, .neras, .truke, .dalle, .lotep, .nusar, .litar, .besub, .cezor, .lokas, .godes, .budak, .vusad, .herad, .berosuce, .gehad, .gusau, .madek, .darus, .tocue, .lapoi, .todar, .dodoc, .bopador, .novasof, .ntuseg, .ndarod, .access, .format, .nelasod, .mogranos, .cosakos, .nvetud, .lotej, .kovasoh, .prandel, .zatrov, .masok, .brusaf, .londec, .krusop, .mtogas, .nasoh, .nacro, .pedro, .nuksus, .vesrato, .masodas, .cetori, .stare, .carote.
In order to decrypt files you need to find several pairs of files. Each pair of files consists of an encrypted file and its original copy. File size over 150kb. After you find several pairs of files, do the following. Open the following link in a new window.
https://decrypter.emsisoft.com/submit/stopdjvu/
You will see a page called STOP Djvu Decryption. An example of this page is given below.
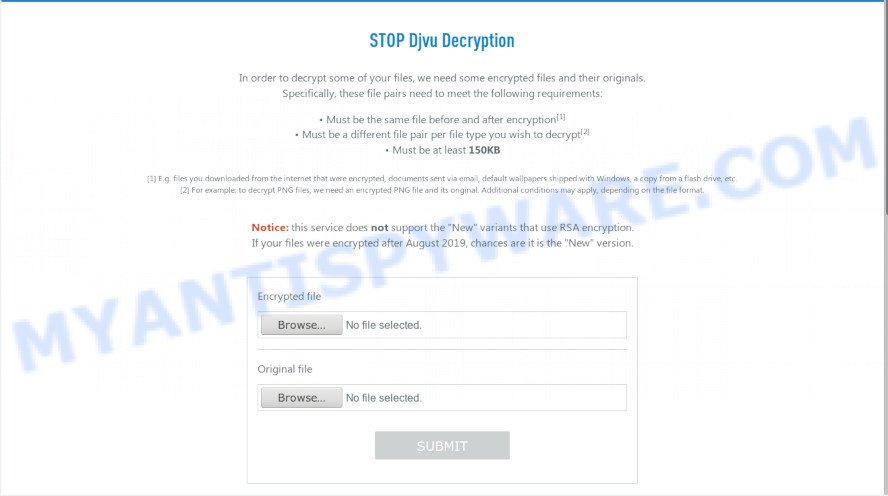
STOP Djvu Decryption
On this page using the Browse button, enter the path to the encrypted file and its original copy, then click the Submit button. After clicking on the Submit button, your files will be uploaded to the server. Then the key search process starts. Please be patient, this process may take some time. As soon as the key is found, an appropriate message will appear on the page and you will be asked to download the decryptor.
Click on the link called “Click here to download the decryptor“. The page from which you can download the decryptor will load. Click the Download button and save the decrypt_STOPDjvu.exe file to your computer.
When the file is downloaded, start it by right-clicking on it and selecting item “Run as Administrator”. When it starts, the Windows can show you UAC Promt, then click Yes. After that, you will be shown the license terms and a small instruction, please read this information to continue.
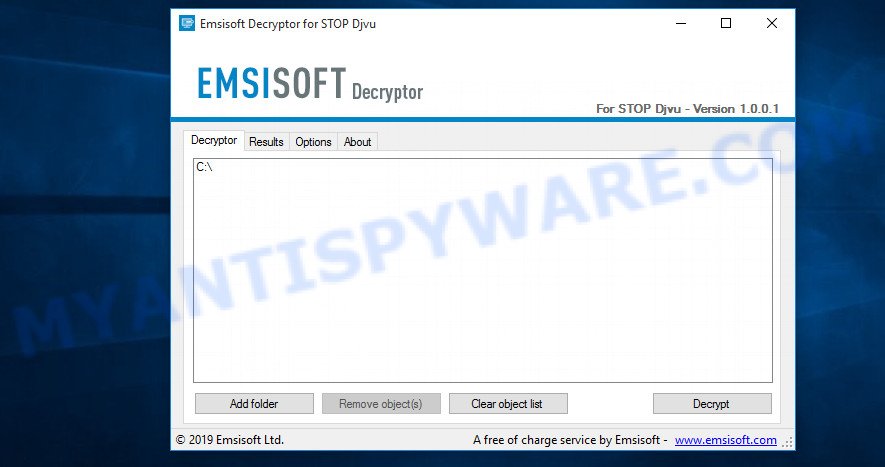
STOP Djvu decryptor
In the main window, select the disk or directory where the encrypted files are located, and then click Decrypt. After that, the decryptor will begin to decrypt the files for which the key was found at the previous stage. If the decryptor skips files, saying that it cannot decrypt them, then you need to again find a couple of files, one of which is encrypted, and the second is its original copy. Then use them to find the decryption key.
3. New Djvu ransomware
The latest version of STOP Djvu ransomware uses the following file extensions: .coharos, .shariz, .gero, .hese, .geno, .xoza, .seto, peta, .moka, .meds, .kvag, .domn, .karl, .nesa, .boot, .kuub, .reco, .bora, .leto, nols, werd, .coot, .derp, .nakw, .meka, .toec, .mosk, .lokf, .peet, grod, .mbed, .kodg, .zobm, .rote, .msop, .hets, .righ, .gesd, .merl, .nbes, .mkos, .piny, .redl, kodc, .nosu, .reha, .topi, .npsg, .btos, .repp, .alka, .bboo, rooe, .mmnn, .ooss, .mool, .nppp, .rezm, .lokd, .foop, .remk, .npsk, opqz, .mado, jope, .mpaj, .lalo, .lezp, .qewe, .mpal, .sqpc, .mzlq, .koti, .covm, .pezi, .nlah, .kkll, .zwer, .nypd, .usam, .tabe, .vawe, .moba, .pykw, .zida, .maas, .repl, .kuus, .erif, .kook, .nile, .oonn, .vari, .boop, .kasp, .ogdo, .npph, .kolz, .copa, .lyli, .moss, .foqe, .mmpa, .efji, .iiss, .jdyi, .vpsh, .agho, .vvoa, .epor, .sglh, .lisp, .weui, .nobu, .igdm, .booa, .omfl, igal, .qlkm, .coos, .wbxd, .pola, .cosd, .plam, .ygkz, .cadq, .ribd, .tirp, .reig, .enfp, .ekvf, .ytbn, .fdcz, .urnb, .lmas, .wrui, .rejg, .pcqq, .igvm, .nusm, .ehiz, .paas, .pahd, .mppq, .qscx, .sspq, .iqll, .ddsg, .piiq, .miis, .neer, .leex, .zqqw, .pooe, .lssr, .zzla, .wwka, .gujd, .ufwj, .moqs, .aeur, .guer, .nooa, .reqg, .hoop, .orkf, .lqqw, .efdc, .wiot, .koom, .rigd, .tisc, .nqsq, .irjg, .vtua, .maql, .zaps, .rugj, .cool, .palq, .stax, .irfk, .qdla, .futm, .utjg, .iisa, .pqgs, .rigj, .robm, .moia, .wnlu, .hgsh, .nnqp, .miia, .loov, .dehd, .nqhd, .vfgj, .maak, .qqqw, .yoqs, .avyu, .cuag, .iips, .qnty, .ccps, .ckae, gcyi, .eucy, .ooii, .rtgf, .fgui, .fgnh, .iiof, .vyia, .vtym, .kqgs, .bpqd, .rguy, .kkia, .mmuz, .wdlo, .kxde, .udla, .mpag, .gtys, .tuid, .uyjh, .msjd, .jhdd, .dmay, .jhbg, .dewd, .sijr, .bbnm, .byya, .ifla, .errz, .dfwe, .fdcv, .nnuz, .qlln, .rrbb, .rryy, .bbyy, .bbii, .bbzz, .hkgt, .efvc, .lltt, .lloo, .llee, .dkrf, .eiur, .ghsd, .jjll, .hhew, .hhwq, .ggew, .ggeo, .ggwq, .ggyu, .ooxa, .oori, .vvew, .vvyu, .vvwq, .vveo, .vvyu, .qqmt. An updated variant of this version appears every few days, the main difference between all variants is the extension of encrypted files. The last variant encrypts files with the .qqmt extension; the personal ID of the victims of this variant starts with 0540.
At the moment, it is possible to decrypt files only in some cases when they are encrypted using an offline key. To decrypt files, download the decryptor using the following link.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Click the Download button and save the decrypt_STOPDjvu.exe file to your computer. Right click to it and select ‘Run as Administrator’. Confirm permission to run the program by pressing the Yes button. Read the license terms and brief instructions. In the main window that opens, select the disk or folder where the encrypted files are located and click the Decrypt button. If the decryptor skips files without decrypting them, then the offline key for them is unknown or they are encrypted with an online key.
This video step-by-step guide will demonstrate How to decrypt files locked by STOP Djvu ransomware.
Finish words
We hope that the set of utilities and services developed by Emsisoft and Michael Gillespie helped you decrypt all the files. If the decryption of the files failed, then do not forget that there is another way to recover your files – is to use data recovery tools. Details on how to recover encrypted files without a key and decryptor are described in the article:
How To Recover Encrypted Files (Ransomware file recovery).


















Your personal ID:
0270Isde5tPtsS0MpXNzwPMVVdAes2p5vTkiPqO8vpGJa4US
DAMLA (5).JPG.agho
this full name. DAMLA (5).JPG.agho
please help me
The “0270Isde5tPtsS0MpXNzwPMVVdAes2p5vTkiPqO8vpGJa4US” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Your personal ID:
0212Asd4a7d6Do45FPxdFGLfVNCR0qT0fJq9MsaQq5gm1elTSRxF
How can I remove this LOKD ransomware?
Use the following guide: https://www.myantispyware.com/2020/03/07/lokd-file-extension-remove-lokd-virus-restore-decrypt-lokd-files/
MY ONLINE KEY IS:
9vWdV9kngdNh9xxN4rlVk2ytQiB8jbR8Xcq8WWQq
CAN YOU PLEASE HELP ME.
The “9vWdV9kngdNh9xxN4rlVk2ytQiB8jbR8Xcq8WWQq” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Your personal ID:
0271Orjkhsks7ljohLWmu0RkliNmm3p17yhGAfBPSyhSTXZW
what should i do ??
The “0271Orjkhsks7ljohLWmu0RkliNmm3p17yhGAfBPSyhSTXZW” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Your personal ID:
0219OIWojlj48T1XYngCoXxelKt4gHsg0KOklPQdRw255VE1awcnx
can i decrypt my files?
The “0219OIWojlj48T1XYngCoXxelKt4gHsg0KOklPQdRw255VE1awcnx” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Your personal ID
rTwTs0jz6AtCUwrdi6calAX3ZbLMhtWFR6MF3WxR
what should i do ??
Can you Help Me PLEASE
The “rTwTs0jz6AtCUwrdi6calAX3ZbLMhtWFR6MF3WxR” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Your personal ID:
0271OrjkRaX5QagQ2cUWBPLErnoWR2JEXLqdL5axikefx8dK
It’s a crisis please help, it’s an online ID , .booa help please
The “0271OrjkRaX5QagQ2cUWBPLErnoWR2JEXLqdL5axikefx8dK” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Your personal ID:
0272omflAsdhki5WH7RYKuv5KfF2oRUPLUoPXjzDnBXCoFXaOqAzRB
It’s a crisis please help, it’s an online ID , .Stop/Djvu help please
The “0272omflAsdhki5WH7RYKuv5KfF2oRUPLUoPXjzDnBXCoFXaOqAzRB” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Can You help me, it’s .RECO
Your personal ID:
0170hYgdfsJKByJV63m89KoajP2cQGvYKofXH8Nooq1Hxqu5XKi
The “0170hYgdfsJKByJV63m89KoajP2cQGvYKofXH8Nooq1Hxqu5XKi” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
0272omflAsdhkiU6nwDCho7CmRIeGBic9GFKpg8nygkdHjvE9JHlGo
The “0272omflAsdhkiU6nwDCho7CmRIeGBic9GFKpg8nygkdHjvE9JHlGo” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
How can i remove remove ransomware QLKM. Not getting help it says ONLINE KEY GENRATED . ENCREPTION IS IMMPOSSIBLE.
PLS HELP
Your files are encrypted with an online key. It is impossible to decrypt the files, since only the authors of the virus have the decryption key. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
my id: ID: t16G9JkV9sfMXbdyi5Wyboac2MgKsVYUIpJdUUrq
this file is imposibile…how i want to resolve this file
The “t16G9JkV9sfMXbdyi5Wyboac2MgKsVYUIpJdUUrq” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Hallo, please help me. Thanku guys
Error: No key for New Variant offline ID: CsZYDF62KIlkLckWzzny1BfJuJoa4wsARweqhCt1
Notice: this ID appears be an offline ID, decryption MAY be possible in the future
Your files are encrypted with an offline key, which means that the files can be decrypted as soon as security researchers obtaine the offline key. When this will happen is unknown. Subscribe to our Facebook/Youtube channel as soon as decryption becomes possible, we will inform our subscribers about it.
My personal ID:
0274aSjeelkzsK8QVX8ob1LJODW9Ycq7SEoFmcGYjDSg3JlWy
Can I decrypt my files?
The “0274aSjeelkzsK8QVX8ob1LJODW9Ycq7SEoFmcGYjDSg3JlWy” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Your personal ID:
0275aSjeeemTh06O5gVBYyQjiorzyOGnNX5jOYxAt5SjNqWYj
Please help, my work pc has been corrupted with the coos malware
The “0275aSjeeemTh06O5gVBYyQjiorzyOGnNX5jOYxAt5SjNqWYj” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
sir please my pc infected by .coos ransomware virus with online key: zOwuuF28V80ZDzE4dI6E1siTfpgrHOM0QmT2yZO2
The “zOwuuF28V80ZDzE4dI6E1siTfpgrHOM0QmT2yZO2” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Personal ID “0O2GPy5Lnmnl6X91rucZOoYO9YNrV3QHZBwUJemp” infected by qklm extension please help me.
The “0O2GPy5Lnmnl6X91rucZOoYO9YNrV3QHZBwUJemp” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Please help me my personal id : esZFmqsO9S5CbFvecEa2WV0g2R3SZb0P4S5oaVt1 infected by igdm extension 🙁
Your files are encrypted with an offline key, which means that the files can be decrypted as soon as security researchers obtaine the offline key. When this will happen is unknown. Subscribe to our Facebook/Youtube channel as soon as decryption becomes possible, we will inform our subscribers about it.
Olá como posso descriptografar?
Your personal ID:
0280oPsw3DrbjhZX7KxXDuvirjSS0fqJOfO1eaXJlpTBGvz3I
The “0280oPsw3DrbjhZX7KxXDuvirjSS0fqJOfO1eaXJlpTBGvz3I” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Your personal ID:
0276oPsw3PT5U8zxUQssVcK9gYtsKxWJuOcBw5kZcxozzUKMy
extension wbxd
The “0276oPsw3PT5U8zxUQssVcK9gYtsKxWJuOcBw5kZcxozzUKMy” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Extension is .ygkz
ID:
0281oPsw37bGqJ7Rb3clHgGS3W2A2PzXCCeYEVjWzISPQfG6e
please help me
Use the following guide: https://www.myantispyware.com/2021/02/11/how-to-remove-ygkz-ransomware-decrypt-ygkz-files/
Extension is .Mool Files
ID:
0209a7d6PLHxjUN1dQr5GFo1U4zfpAZdVryLMz9Aou5atkc7
please help me
The “0209a7d6PLHxjUN1dQr5GFo1U4zfpAZdVryLMz9Aou5atkc7” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
.reig files
ID : 0285oPsw3L2yJQSnXxKjAublQXyW9yLEqnd8q3Fsa2UAKwoa
help 🙁
The “0285oPsw3L2yJQSnXxKjAublQXyW9yLEqnd8q3Fsa2UAKwoa” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
Hi, Please Help me..I got RIBD virus, How to decrypt ?
online key User ID :0284oPsw3zXIDOtIyDIqdTV1YK4zZj75TFTll4bsMkgj2XZbr
Thanks A lot..
Your files are encrypted with an online key. It is impossible to decrypt the files, since only the authors of the virus have the decryption key. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.
hZcC4PEfaqDNIXxy0ProMPOAk3JS3K1JoUqoq0t1
File: C:\Users\pc\Desktop\hafsa\Albüm 5\20180129_223912.jpg.kolz
Error: No key for New Variant offline ID: hZcC4PEfaqDNIXxy0ProMPOAk3JS3K1JoUqoq0t1
Notice: this ID appears be an offline ID, decryption MAY be possible in the future
Hello! I got ENFP extension on my files. I cannot find the malware in startup perhaps it has been removed by the several anti virus / anti malware apps that I have installed and run. Can I decrypt my files with Emisoft? Most of them are .bin files from my games. I can still run them, though, but of course, I need them decrypted. Please help me thank you.
Your files are encrypted with an offline key, which means that the files can be decrypted as soon as security researchers obtaine the offline key. When this will happen is unknown. Subscribe to our Facebook/Youtube channel as soon as decryption becomes possible, we will inform our subscribers about it.
Hi, Please Help me… I got ENFP extension virus. Key user ID :CarNPUyfZ1s7ymQzPWLSV5G9jg5gdAlIOjcnSgvc
Thanking you in advance.
Your files are encrypted with an online key. It is impossible to decrypt the files, since only the authors of the virus have the decryption key. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.