What is .Mbed file
.Mbed file extension is a file extension that is associated with the new malware from STOP (djvu) family. Variant ‘Mbed’ shares the characteristics of previous versions of this ransomware. It encrypts files and then renames them. Encrypted files will have a new filename consisting of their old filename and the .mbed extension added to the right. The authors of the virus require a ransom in exchange for a pair – a key and a decryptor, which are necessary for decrypting the files. Fortunately, a group of security researchers created a free decryptor that can help virus victims decrypt files and unlock their contents for free. Scroll down to find out more about the decryptor, where to download it and how to use it to decrypt .mbed files.
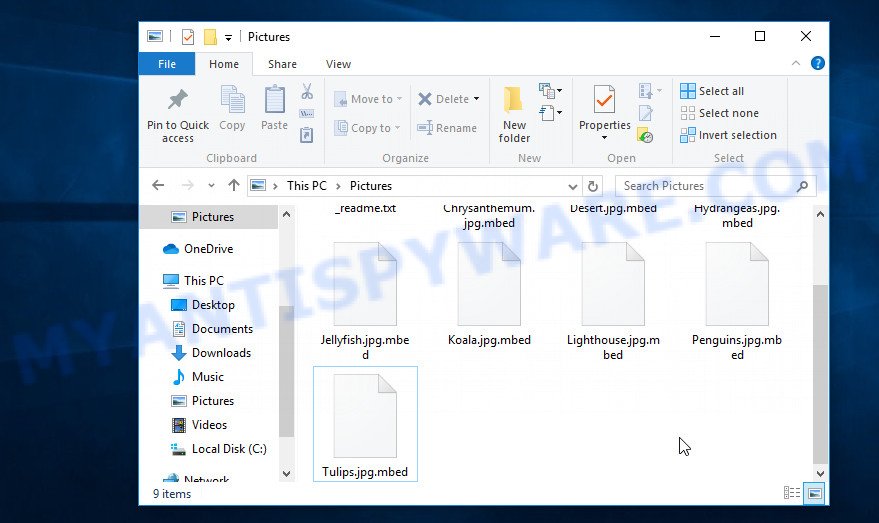
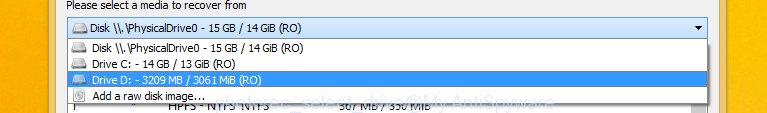
Screenshot of files encrypted by Mbed virus (‘.mbed’ file extension)
What is Mbed virus
Mbed virus is a malware program created by criminals to encrypt files on a victim’s computer. A strong cryptographic algorithm and a long key are used to encrypt files. This eliminates the possibility of decrypting files without a key and decryptor, which are in the hands of attackers. Encrypted files are useless, their contents cannot be read or used in any way.
Mbed was created to infect computers running Windows OS. Most often, victims infect their computer by downloading and installing the virus that is disguised as free software, cracks, key generators, torrents files and so on. Upon execution, the downloaded file installs a virus instance on the victim’s computer.
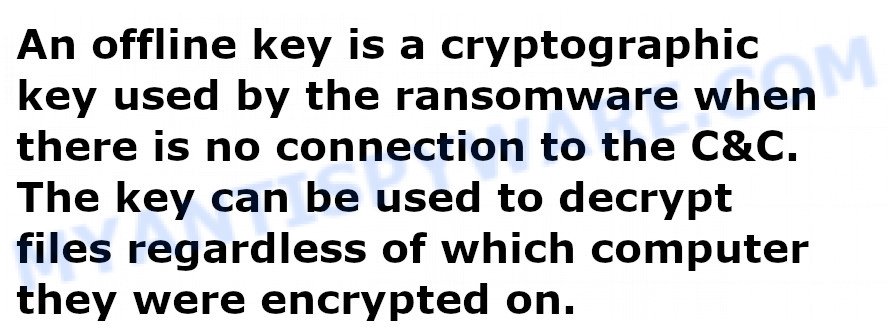
Once installed, Mbed virus collects information about the victim’s computer and then tries to establish a connection with its command-and-control (C&C) server. If the connection is successful, then the virus uses the so-called ‘online key’ to encrypt files. This key is unique to each computer. If a connection to its C&C has not been established, Mbed uses the so-called ‘offline key’. This key is the same for all victims and for all infected computers.
All files on the victim’s computer are the target of Mbed virus. Even data that is on USB drive or cloud storage can be encrypted. The virus skips and does not encrypt files that are in the Windows OS system directories, as well as files with the extension .ini, .bat, .sys, .dll, .lnk and the filename ‘_readme.txt’. All other user files will be encrypted, regardless of what is in the files. For example, files of the following types can be encrypted:
.0, .mp4, .3fr, .zip, .wpw, .wpe, .mov, .xyw, .wps, .wotreplay, .rim, .pptx, .raf, .wp6, .wb2, .apk, .lvl, .xar, .re4, .bay, .iwi, .7z, .xlsx, .slm, .pkpass, .xwp, .itl, .webp, .lrf, .wcf, .wot, .pfx, .rofl, .mddata, .pem, .sum, .xbdoc, .rw2, .dazip, .xdb, .zdb, .wma, .wpt, .cfr, .odm, .pst, .x3f, .xy3, .ztmp, .mef, .wire, .gho, .z, .xx, .jpe, .bik, .kf, .xls, .nrw, .xml, .ybk, .docm, .doc, .x3d, .esm, .zi, .m2, .map, .crt, .xlsm, .wgz, .mrwref, .ncf, .wbmp, .das, .mdf, .accdb, .m3u, .forge, .2bp, .bar, .xls, .zw, .dng, .wbk, .dbf, .p12, .rwl, .wmo, .svg, .pptm, .upk, .xlk, .xmmap, .pdf, .xf, .wsc, .rar, .wav, .bc7, .arw, .bsa, .rtf, .wmf, .big, .t13, .itm, .icxs, .vpk, .wn, .xld, .menu, .sie, .mlx, .sis, .snx, .mpqge, .yml, .xxx, .vtf, .desc, .xmind, .odc, .wp, .wpb, .ibank, .rb, .wdp, .vdf, .ws, .wbd, .ltx, .png, .y, .ppt, .wp5, .py, .p7c, .docx, .zabw, .pef, .qdf, .fos, .wbz, .wma, .flv, .srf, .indd, .fpk, .bkp, .dcr, .litemod, .orf, .cdr, .wp7, .js, .xll, .ods, .sb, .z3d, .asset, .jpeg, .pdd, .mdb, .db0, .ntl, .tax, .itdb, .sr2, .xbplate, .m4a, .3dm, .txt, .webdoc, .sav, .ff, .wm, .hkx, .wp4, .cr2, .xyp, .ptx, .d3dbsp, .vpp_pc, .mdbackup, .1, .iwd, .t12, .3ds, .bkf, .1st, .x, .odb, .sid, .gdb, .vfs0, .ysp, .vcf, .cas, .wmd, .hplg, .zdc, .layout, .raw, .kdb, wallet, .epk, .p7b, .wbm, .fsh, .xlsb, .avi, .wmv, .r3d, .yal, .x3f, .sql, .wpl, .sidd, .wpd, .wri, .rgss3a, .jpg, .dmp, .zip, .hvpl, .wsd, .srw, .der, .wpg, .wdb, .xlsm, .qic, .tor, .psk, .sidn, .mcmeta, .cer, .blob, .wpa, .xlgc, .erf, .xdl, .hkdb, .wmv, .psd, .wsh, .xlsx, .wpd
Mbed virus quickly encrypts files on the infected computer, and does this file by file in each directory that it finds on the drives connected to the computer. Encrypted files are easily visible, they have a new .mbed extension and a blank icon. If the user tries to open such files, the Windows OS will report that it does not know how to do this and cannot find a program that can read files of this type. In addition to encrypted files, in each directory the victim will find another file. This file is named ‘_readme.txt’ and it contains a message from the authors of Mbed virus.
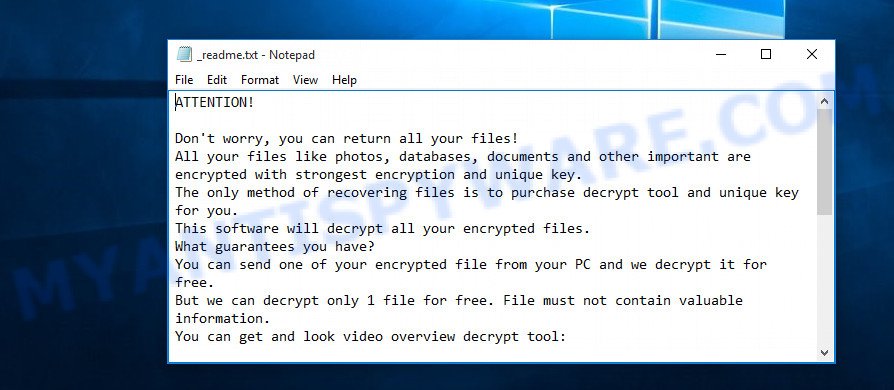
Screenshot of the contents of ‘_readme.txt’ file (Mbed ransom note).
The file ‘_readme.txt’ is a ransom note. In it, criminals report that the victim’s files are encrypted and the only way to decrypt them is to use a unique key and decryptor. Attackers demand a ransom in exchange for this key and decryptor. The ransom amount is $490 if the victim pays for it within 72 hours. Otherwise, the ransom is doubled, and becomes $980. Criminals do not leave any information on how to pay the ransom. They suggest that the victim write an email letter to them at one of the addresses listed in the ransom note. Mbed authors promise to decrypt one file for free, but will do so if the file is small and does not contain any important information. Even if one file is decrypted, criminals cannot be trusted, there is no guarantee that after receiving the ransom they will provide the key and decryptor necessary for decrypting the files.
Threat Summary
| Name | Mbed |
| Type | Ransomware, Filecoder, File locker, Crypto virus, Crypto malware |
| Encrypted files extension | .mbed |
| Ransom note | _readme.txt |
| Contact | restoredatahelp@firemail.cc, gorentos@bitmessage.ch |
| Ransom amount | $490,$980 in Bitcoins |
| Detection Names | Trojan: Encoder, Trojan.RansomCrypted, UDS.DangerousObject.MultiGeneric, Trojan: Win32Kryptik, FileRepMalware, TRCrypt.Agent, Malware: Win32Ransom |
| Symptoms | Files encrypted with .mbed file extension. Unable to open documents, photos and music. Your personal files have a wrong name, suffix or extension, or don’t look right when you open them. Your file directories contain a ‘ransom note’ file that is usually a _readme.txt file. |
| Distribution methods | Torrents files. Phishing emails. Malicious downloads. Cracks. Social media. Activators. Adware. |
| Removal | Mbed virus removal guide |
| Decryption | Free Mbed Decryptor |
In a ransom note, criminals report that encrypted files cannot be decrypted without a key and a decryptor. Unfortunately, this is true, the encryption algorithm that uses the virus locks the contents of encrypted files. Therefore, in any case, in order to decrypt the files, the victim needs a key and a decryptor.
Fortunately for each of the victims of Mbed virus, there is a universal decryptor that can decrypt files encrypted with different versions of STOP (Djvu) ransomware. And since Mbed is one of the variants of STOP (Djvu), this decryptor can decrypt .mbed files. The only limitation of this decryptor is that it can decrypt files that were encrypted with an offline key. But even if the decryptor cannot decrypt the files, then there are several alternative ways to recover the data in the encrypted files.
How to remove Mbed and Decrypt .mbed files
If you find files with .mbed extension on your computer, then the computer is the victim of ransomware attack. To unlock the contents of encrypted files, you need to take several steps. First you need to make sure that the computer does not contain malicious software, and only after that proceed to decrypt the files. In case when the decryption of the files failed, you need to use step 3, try to restore the files to their original state using several alternative methods. These methods do not require a key and decryptor. In order not to miss any part of the instructions, we recommend that you print it or open it on your smartphone.
Remove Mbed ransomware virus
The first thing we advise every victim of Mbed virus is to check the computer for ransomware and other malware. This step is better not to skip. The reason is simple, if you do not remove Mbed virus, then after the files are decrypted, it will encrypt them again. Moreover, do not forget that active malware is a breach in protecting your computer, criminals can access the entire computer, control your computer, or use your computer to hack into other computers.
We recommend using free malware removal tools to detect and remove Mbed ransomware. Moreover, it is advisable to check the computer not with one tool but with two or more. So you can be sure that the virus is completely removed.
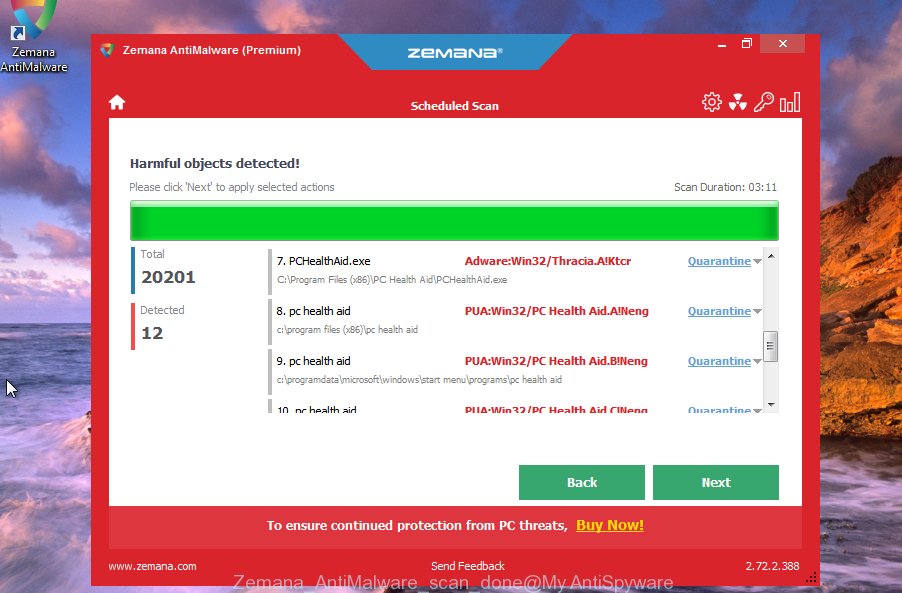
Use Zemana AntiMalware to remove Mbed ransomware virus
Zemana AntiMalware (ZAM) is a utility with which you can start to find and remove Mbed virus. Of course, this program can remove not only ransomware, but also other active malicious software, including Trojans, spyware, adware, PUPs, worms. You can remove all found malware for free by simply pressing one key. More importantly, if you have problems with Mbed removal, this program provides free online support.
- Visit the page linked below to download the latest version of Zemana AntiMalware.
Zemana AntiMalware
165500 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
- Double click on the downloaded file Zemana.AntiMalware.Setup.
- Follow the prompts. Once the installation is finished, Zemana will run automatically.
- Click ‘Scan’ to perform a system scan for Mbed virus.
- After Zemana has finished scanning your PC, click ‘Next’ button.
- Restart your PC to complete Mbed virus removal process.
Remove Mbed ransomware with MalwareBytes
Another option to remove Mbed ransomware is to use a program called MalwareBytes. We recommend this program to readers of our site for more than 10 years. This program will help you to fully scan the computer, find all parts of Mbed virus and remove them for free.
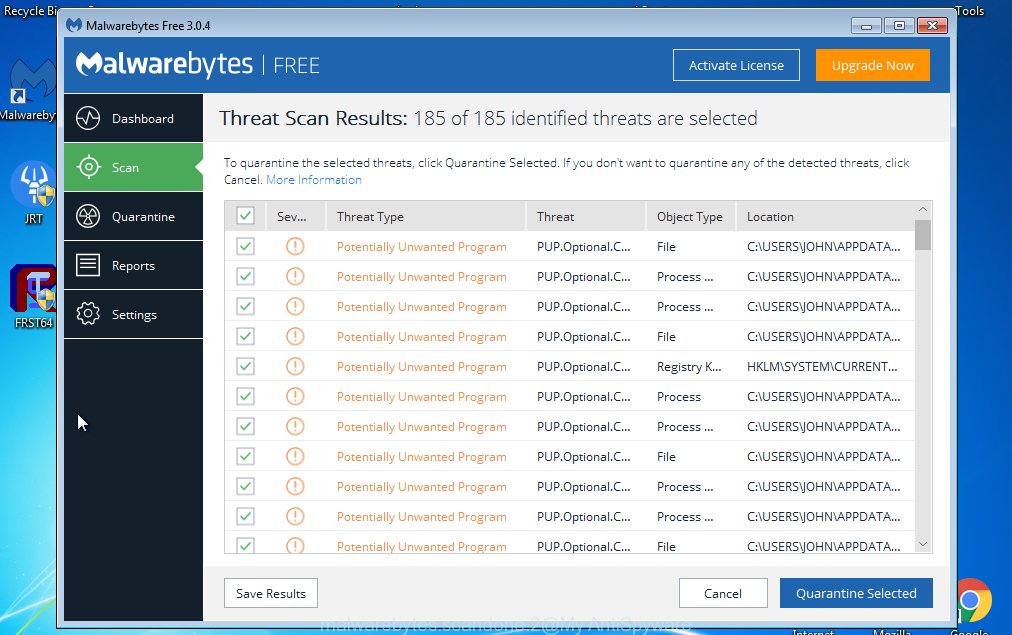
- Download MalwareBytes from the link below.
Malwarebytes Anti-malware
327717 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
- Close all programs and run the downloaded file.
- Follow the prompts.
- Once install is complete, click the “Scan Now” button.
- After the checking is finished, MalwareBytes will open a list of the found malware.
- Press “Quarantine Selected” button. Malwarebytes will now remove Mbed related folders, files and registry keys.
To learn more about how to use MalwareBytes to remove Mbed ransomware, we recommend that you read the following guide: How to use MalwareBytes.
Use Kaspersky virus removal tool to remove Mbed virus
Kaspersky virus removal tool (KVRT) is a free malware removal tool. It can detect and remove ransomware, trojans, spyware, adware, worms, and other security threats. KVRT is powerful enough to find and remove malicious registry entries and files that are hidden on the system.
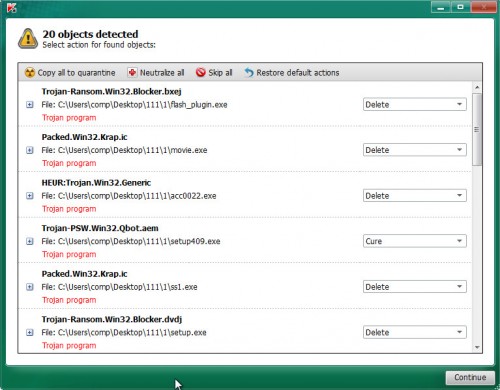
- Download Kaspersky virus removal tool from the link below.
Kaspersky virus removal tool
129491 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
- Double-click on the downloaded file, follow the prompts.
- Once initialization process is finished, click Start scan button to start scanning the system for Mbed virus.
- When the scan is complete, click the Continue button to remove the found malware.
If you want to know more about Kaspersky virus removal tool, how to use it to remove Mbed virus, then read the following article: How to use Kaspersky virus removal tool.
How to decrypt .mbed files
Files with extension .mbed are encrypted files. These files can only be decrypted using a key-decryptor pair. It is not possible to decrypt files in another way. The authors of Mbed virus demand a ransom for the key and the decryptor. Of course, no one can guarantee that after paying the ransom, the victim will be able to decrypt the encrypted files. Security experts do not recommend paying a ransom, as this pushes criminals to create a new ransomware.
Fortunately for all victims of Mbed virus, there is a free decryptor. It allows each victim to decrypt files encrypted with STOP ransomware. And since Mbed is one of the variants of this ransomware, this decryptor can be used to decrypt .mbed files.
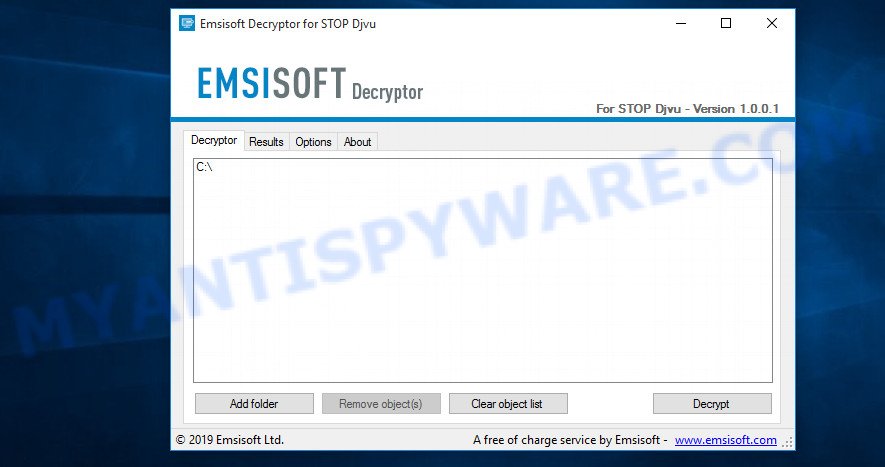
STOP (Mbed) decryptor
To decrypt .mbed files, use free STOP (Mbed) decryptor
- Visit the page linked below to download STOP (Djvu) decryptor.
STOP Djvu decryptor - Scroll down to ‘New Djvu ransomware’ section.
- Click the download link and save the ‘decrypt_STOPDjvu.exe’ file to your desktop.
- Run decrypt_STOPDjvu.exe, read the license terms and instructions.
- On the ‘Decryptor’ tab, using the ‘Add a folder’ button, add the directory or disk where the encrypted files are located.
- Click the ‘Decrypt’ button.
STOP (Mbed) decryptor is a fantastic program that allows everyone to decrypt files for free. Unfortunately, at the moment, this decryptor can only decrypt files encrypted with ‘offline key’. If the files on the victim’s computer are encrypted with an online key, then they will be skipped, these files cannot yet be decrypted. Online keys are unique to each computer and cannot be determined by security researchers. Only the criminals own them.
How to find out which key was used to encrypt files
Since Mbed decryptor only decrypts files encrypted with the offline key, each virus victim needs to find out which key was used to encrypt the files. Determining the type of key used is not difficult. Below we give two ways. Use any of them.
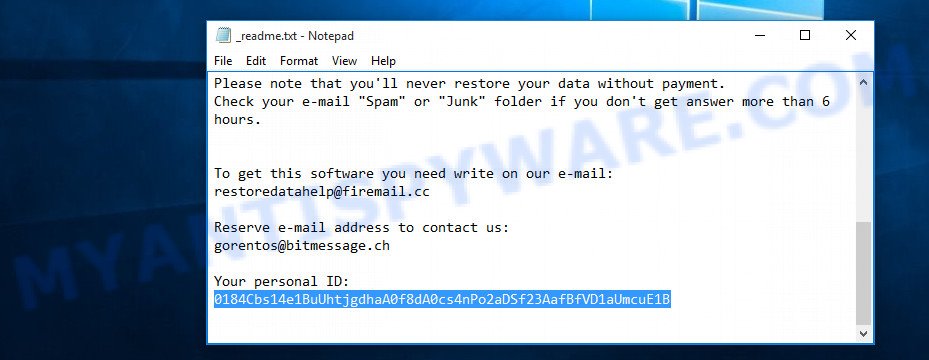
Personal ID is highlighted here
Find out the type of key using ‘_readme.txt’ file
- Open the ransom demand message (‘_readme.txt’ file).
- Scroll down to the end of the file.
- There you will see a line with the text ‘Your personal ID’.
- Below is a line of characters that starts with ‘0184’ – this is your personal id.
Find out the type of key using ‘PersonalID.txt’ file
- Open disk C.
- Open directory ‘SystemID’.
- Open file named ‘PersonalID.txt’. This file lists ‘Personal ID’s that match the keys that the virus used to encrypt files.
This ID is not a key, it is a set of characters by which everyone can find out which key was used to encrypt files. If the ID ends with ‘t1’, then your files are encrypted with an offline key. If the ID does not end with ‘t1’, then Mbed used an online key. If you could not understand which key was used to encrypt your files, then we can help you. Just write a request in the comments below.
Error: Unable to decrypt file with ID
If during decryption of files the decryptor reports ‘Error: Unable to decrypt file with ID’, skips files without decrypting them, then two cases are possible why this happens:
- mbed files are encrypted with an ‘online key’, in this case, you need to use alternative methods to restore the contents of encrypted files;
- mbed files are encrypted with an ‘offline key’, but the key itself has not yet been found by security researchers, in this case, you need to be patient and wait a while, in addition, you can also use alternative ways for recovering encrypted data;
How to restore .mbed files
Fortunately, in addition to using STOP (Mbed) decryptor, there are several alternative ways to recover the contents of encrypted files. However, if you have not tried the decryptor, then try it first by following step 2 of this instruction, and then return here.
Alternative methods of file recovery do not use decryption, so there is no need for a key and decryptor. Before you begin, you must be 100% sure that the computer does not have active ransomware. Therefore, if you have not yet checked your computer for malware, do it right now, return to step 1.
Use ShadowExplorer to restore .mbed files
In some cases, you have a chance to restore the files that were encrypted by Mbed virus. This is possible due to the use of a free utility called ShadowExplorer. It is a program that developed to obtain ‘shadow copies’ of files.
Visit the page linked below to download the latest version of ShadowExplorer for Windows. Save it on your Desktop.
440038 downloads
Author: ShadowExplorer.com
Category: Security tools
Update: September 15, 2019
Once the download is done, open a directory in which you saved it. Right click to ShadowExplorer-0.9-portable and select Extract all. Follow the prompts. Next please open the ShadowExplorerPortable folder similar to the one below.
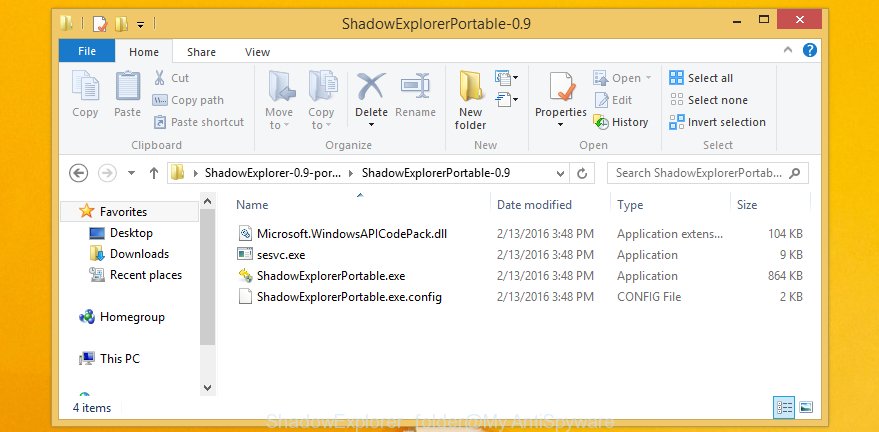
Double click ShadowExplorerPortable to start it. You will see the a window as on the image below.
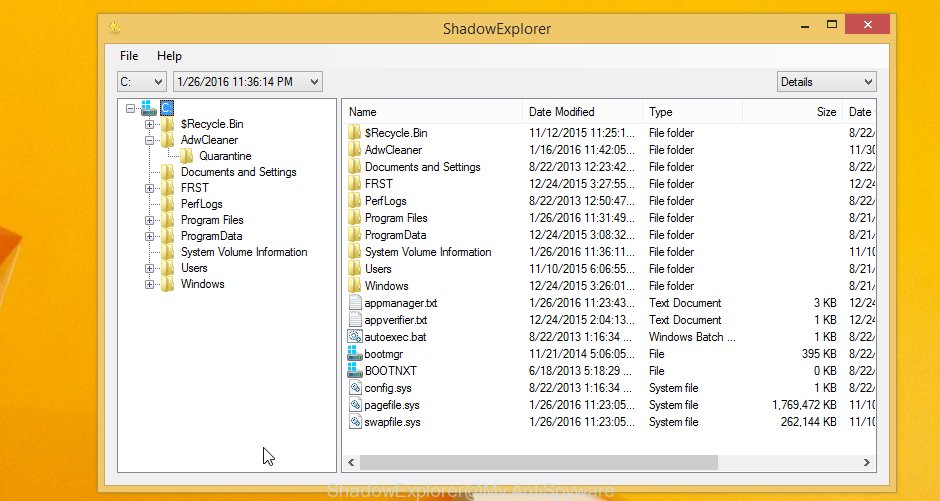
In top left corner, select a Drive where encrypted photos, documents and music are stored and a latest restore point as displayed in the figure below (1 – drive, 2 – restore point).
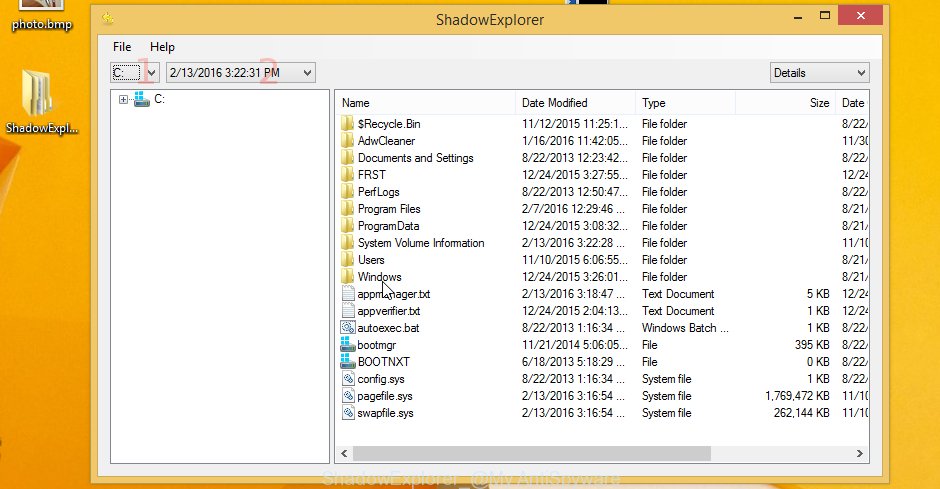
On right panel look for a file that you wish to recover, right click to it and select Export like the one below.

Recover .mbed files with PhotoRec
Another alternative way to recover the contents of encrypted files is to use data recovery software. We suggest you pay attention to the program called PhotoRec. Photo Rec has all the necessary features for searching and restoring files and it is free.
Download PhotoRec on your Windows Desktop from the link below.
Once downloading is done, open a directory in which you saved it. Right click to testdisk-7.0.win and choose Extract all. Follow the prompts. Next please open the testdisk-7.0 folder like the one below.

Double click on qphotorec_win to run PhotoRec for Microsoft Windows. It’ll display a screen similar to the one below.
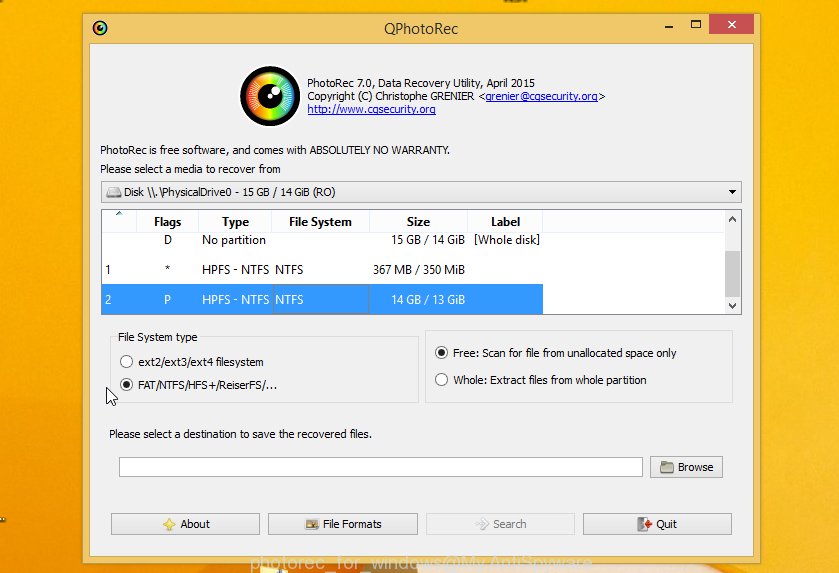
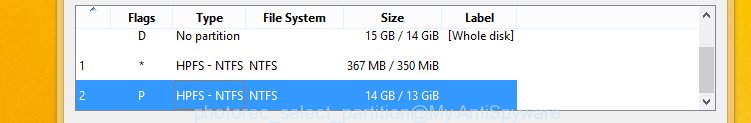
Choose a drive to recover as shown in the following example.
You will see a list of available partitions. Select a partition that holds encrypted files as displayed on the image below.
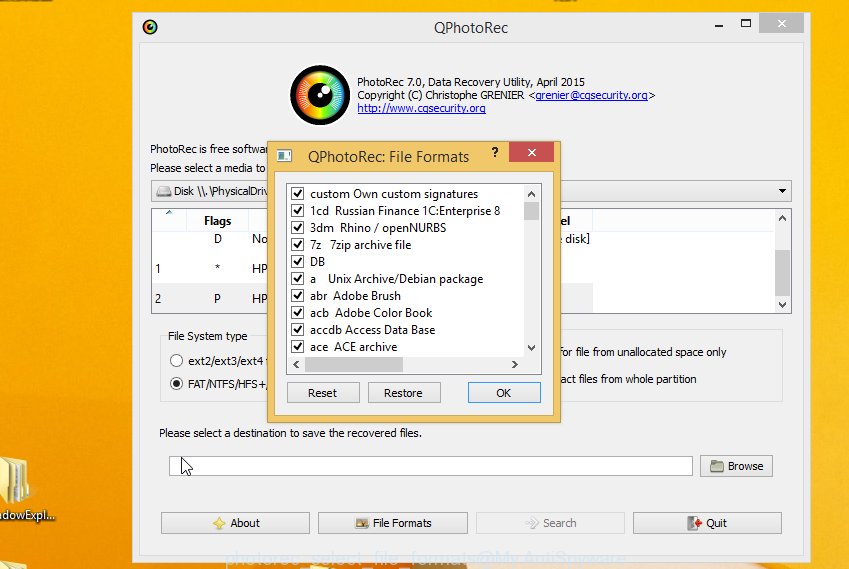
Click File Formats button and specify file types to recover. You can to enable or disable the restore of certain file types. When this is finished, click OK button.
Next, press Browse button to choose where restored files should be written, then click Search.
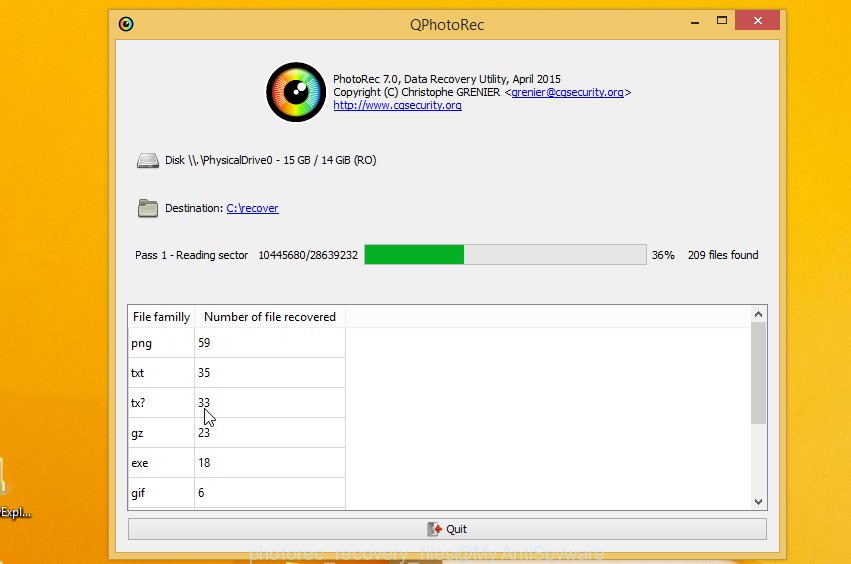
Count of recovered files is updated in real time. All recovered documents, photos and music are written in a folder that you have chosen on the previous step. You can to access the files even if the recovery process is not finished.
When the restore is done, press on Quit button. Next, open the directory where restored photos, documents and music are stored. You will see a contents as displayed on the image below.
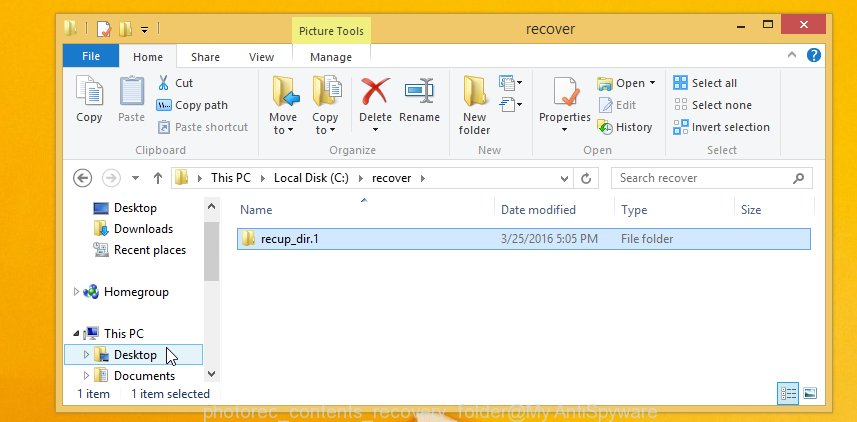
All recovered files are written in recup_dir.1, recup_dir.2 … sub-directories. If you’re searching for a specific file, then you can to sort your recovered files by extension and/or date/time.
Finish words
“Mbed file extension. Remove Mbed virus. Restore, Decrypt .mbed files.” guide was created to help all victims of Mbed virus. We tried to give answers to the following questions: how to remove ransomware; how to decrypt .mbed files; how to recover files, if the decryptor does not help; what is an online key and what is an offline key. We hope that the information presented in this manual has helped you.
If you have questions, then write to us, leaving a comment below. If you need more help with Mbed related issues, go to here.




















hi, please help me decrypt my data
personal ID: 0184Asd374y5hJIEOGtmBF5w1f7DuQ7OQ1jz7vdbO5M5wb7uIRti
0184Asd374y5p5o4K4H8huLjkprN6oHj2IdZrE4Qowgorld0jSYBLLWAIkqG3qNfVh3kf8tNIFZAcbo4QRPKglWj5tRM
0184Asd374y5hJIEOGtmBF5w1f7DuQ7OQ1jz7vdbO5M5wb7uIRti
These IDs are related to online keys, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.
help this is my personal id 0184Asd374y5DJ3O4UTPDZnADCeHQFC3wN8lxRo701cIL1dnPdCv
The “0184Asd374y5DJ3O4UTPDZnADCeHQFC3wN8lxRo701cIL1dnPdCv” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the following guide: How to recover ransomware encrypted files.