What is Support@freshingmail.top?
Support@freshingmail.top is associated with cybercriminals who deploy STOP (DJVU) ransomware. This ransomware is a type of malware that encrypts files on the victim’s computer, effectively locking them out of their data, and demands a ransom for the decryption key. The attack can lead to significant data loss and financial harm. The ransomware changes file names by adding new extensions, such as .Cdqw or .Cdmx. It also creates “_readme.txt” files, which contain the ransom note. For example, a file originally named “document.docx” would be renamed to “document.docx.cdqw”, and similarly, “image.jpg” would become “image.jpg.cdqw”, “invoice.pdf” to “invoice.pdf.cdqw”, and so on.
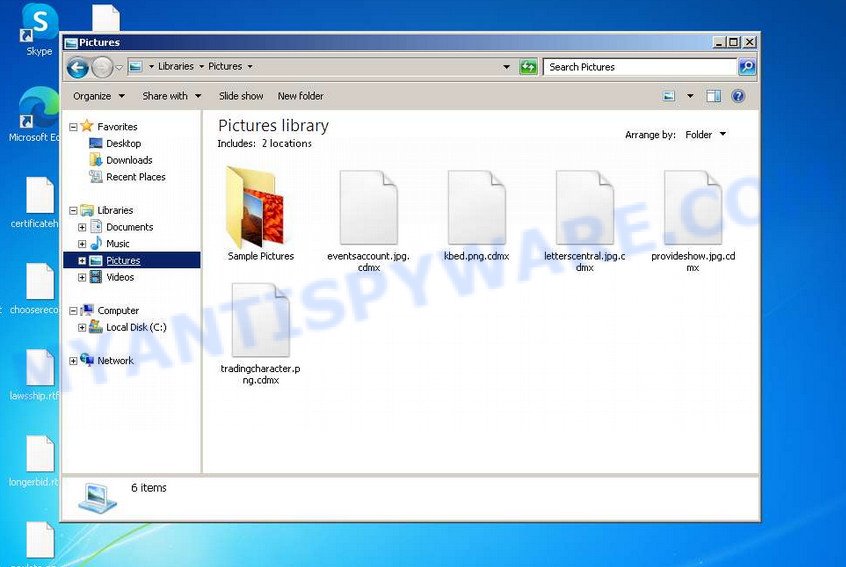
Screenshot of files encrypted by the Support@freshingmail.top virus
QUICK LINKS
- What is Support@freshingmail.top?
- Remove Support@freshingmail.top virus (ransomware)
- Decrypt encrypted files
- Restore encrypted files
- Video Guide
Support@freshingmail.top ransomware in detail
The Support@freshingmail.top ransomware spreads through malicious downloads found on torrent sites and phishing websites. When executed, it creates a directory in the Windows system folder and replicates itself there. The malware then gathers data about the infected computer and alters system settings to ensure it launches automatically with each system startup or reboot.
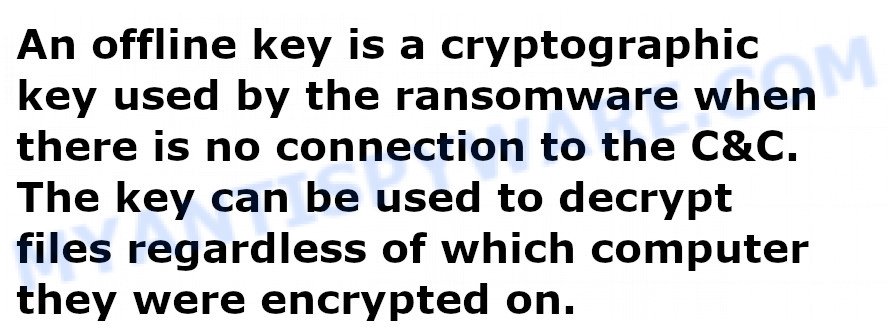
The ransomware’s next step is to try connecting with its command and control (C&C) server. Successful connection allows the ransomware to receive a unique encryption key (termed the “online key”) for file encryption. Additionally, it may receive further commands and files to execute on the victim’s computer. If the ransomware fails to connect to the C&C server, it resorts to a pre-set key known as the “offline key”. The distinction between “online” and “offline” keys is crucial. An online key is specific to each infected computer, meaning a decryption key from one system cannot decrypt files on another. Conversely, the offline key is identical across all infections, allowing for a universal decryption solution.
Once the Support@freshingmail.top ransomware obtains the encryption key, it begins the file encryption process. It encrypts each file individually, targeting files regardless of their location—whether on internal drives, flash drives, external media, or cloud storage. However, there are exceptions: the virus does not encrypt files in the Windows system directories or files with specific extensions like ‘.lnk’, ‘.bat’, ‘.ini’, ‘.sys’, ‘.dll’. Additionally, it avoids encrypting files named ‘_readme.txt’. As a result, almost all user data, including documents, pictures, databases, archives, and various other file types, become encrypted.
crt, .wbmp, .rw2, .mdbackup, .xyp, .zdb, .wpb, .mlx, .vfs0, .ods, .p12, .vcf, .kdb, .xpm, .gho, .3dm, .pptm, .py, .lvl, .wbm, .vtf, .webdoc, .xlsm, .xdl, .w3x, .wps, .zip, .itm, .ptx, .wb2, .cdr, .wn, .bik, .pdf, .cfr, .webp, .wotreplay, .asset, .docx, .cr2, .map, .yml, .pfx, .wsc, .crw, .docm, .bkf, .pst, .rb, .pptx, .desc, .7z, .re4, .dxg, .upk, .ysp, .wri, .psd, .y, .doc, .zdc, .ybk, .mcmeta, .xar, .psk, .dba, .erf, .menu, .wdb, .jpg, .accdb, .p7b, .wpt, .xmmap, .1st, .tax, .fos, .xxx, .ws, .xlsx, .3ds, .layout, .sis, .qdf, .das, .hkdb, .jpeg, .ibank, .mrwref, .cas, .bsa, .js, .pkpass, .vdf, .sr2, .x3f, .big, .wmv, .wbz, .xwp, .epk, .ztmp, .xlgc, .sid, .xlsm, .sidn, .z, .pak, .wbk, .xf, .wm, .mpqge, .mdb, .wps, .snx, .xlsb, .arch00, .csv, .lrf, .sb, .pem, .dbf, .ff, .syncdb, .xbdoc, .wp5, .forge, .sie, .hplg, .bc6, .wma, .flv, .indd, .zif, .m3u, .odp, .odm, .svg, .xll, .wp7, .wdp, .dcr, .t12, .wsd, .mdf, .raf, .wav, .sidd, .yal, .wgz, .fpk, .rtf, .rim, .arw, .lbf, .xx, .apk, .qic, .xdb, .mov, .slm, .odc, .xlsx, .wbd, .sum, .wpg, .pef, wallet, .wcf, .2bp, .3fr, .wmf, .wma, .wpd, .dazip, .zi, .d3dbsp, .1, .wot, .eps, .wpd, .ppt, .srf, .txt, .srw, .wpa, .sav, .xyw, .xmind, .gdb, .wmv, .zabw, .rwl, .rar, .m2, .orf, .wpe, .xml, .ltx, .mddata, .cer, .z3d, .vpp_pc, .odt, .fsh, .sql, .kdc
The Support@freshingmail.top ransomware renames each file it encrypts by adding a new extension to the file’s original name. For example, an encrypted file originally named ‘image.jpg’ would be renamed to ‘image.jpg.mzqw’. To maximize efficiency and encrypt as many files as possible in the shortest amount of time, the ransomware only encrypts the first 154 kb of each file, rather than the entire file. This partial encryption approach is applied file by file. Once all files in a directory are encrypted, the ransomware places a new file in that directory, named ‘_readme.txt’, which contains the ransom demand and instructions.
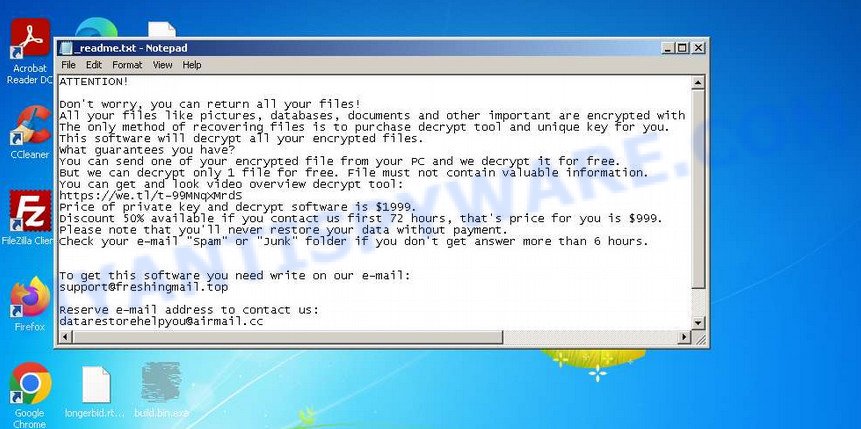
Screenshot of the contents of ‘_readme.txt’ file (ransom demand message)
The ‘_readme.txt’ file placed by the Support@freshingmail.top ransomware in encrypted directories serves as a ransom note from the malware’s creators. In this note, the attackers inform the victim that their files have been encrypted. They state that the only way to decrypt the files is to purchase a decryption key and tool from them. The initial ransom amount is set at $1999, but the attackers offer a 50% discount, reducing the ransom to $999, if the payment is made within 72 hours of the attack.
Additionally, the criminals propose to decrypt one file for free as a demonstration of their capability. To avail of this offer, the victim is instructed to send the file to an email address provided in the ransom note. However, it’s important to note that decrypting one file successfully does not guarantee that all files can be decrypted, even after the ransom is paid.
Text presented in the “_readme.txt” file:
ATTENTION!
Don’t worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-99MNqXMrdS
Price of private key and decrypt software is $1999.
Discount 50% available if you contact us first 72 hours, that’s price for you is $999.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshingmail.topReserve e-mail address to contact us:
datarestorehelpyou@airmail.ccYour personal ID:
As mentioned earlier, the Support@freshingmail.top virus is a type of STOP ransomware. Consequently, victims can use the Emsisoft decryptor, which is a free tool designed to decrypt files affected by this ransomware. While there’s a possibility that the decryptor might not work in all cases, there are alternative methods available for attempting to restore the contents of the encrypted files.
For detailed guidance on decrypting files, refer to the section titled ‘How to decrypt encrypted files’. It’s important to read the entire manual thoroughly to understand the process fully. For convenience and ease of following the instructions, consider printing the manual or accessing it on your smartphone.
Threat Summary
| Name | Support@freshingmail.top ransomware |
| Type | Crypto virus, File locker, Ransomware, Filecoder, Crypto malware |
| File extension | .Cdqw, .Cdmx |
| Ransom note | _readme.txt |
| Contact | support@freshingmail.top, datarestorehelpyou@airmail.cc |
| Ransom amount | $999 or $1999 in Bitcoins |
| Detection Names | W32/Kryptik.HCVW!tr, PWSX-gen [Trj], Gen:Heur.Mint.Zard.52, Ransom.Stop.P5, BehavesLike.Win32.Lockbit.cc, Trojan.Win32.Save.a, Trojan:Win32/Sabsik.FL.B!ml, VHO:Backdoor.Win32.Convagent.gen |
| Symptoms | Your files fail to open. Your files have a wrong name, suffix or extension, or don’t look right when you open them. Files called such as ”, ‘READ-ME’, ‘_open me’, _DECRYPT YOUR FILES’ or ‘_Your files have been encrypted” in every folder with an encrypted file. Ransom demanding message on your desktop. |
| Distribution methods | Spam mails that contain malicious links. Exploit kits (cybercriminals use ransomware virus packaged in an ‘exploit kit’ that can find a vulnerability in Microsoft Windows OS, PDF reader, Adobe Flash Player, Web browser). Social media posts (they can be used to entice users to download malicious software with a built-in ransomware downloader or click a malicious link). Cybercriminals use misleading advertisements to distribute malware with no user interaction required. |
| Removal | Support@freshingmail.top ransomware removal guide |
| Decryption | Ransomware Decrypt Tool |
How to remove Support@freshingmail.top virus (ransomware)
Before attempting to decrypt or restore files encrypted by the Support@freshingmail.top ransomware, it is crucial to first remove the ransomware from your system. If not removed, the ransomware could re-encrypt any files that you manage to restore. Stopping the ransomware from operating is a necessary step and can be achieved with some effort.
Alternatively, you can conduct a comprehensive system scan using free malware removal tools that are specifically designed to detect and eliminate ransomware infections. Such tools can be found at free malware removal tools. It’s important to read the entire manual for these tools thoroughly to understand the removal process. For ease of access and convenience, consider printing the manual or viewing it on your smartphone.
Scanning your computer for malware is crucial, especially since security researchers have discovered that spyware might be installed alongside the ransomware in the case of the Support@freshingmail.top virus. Spyware poses a significant security risk as it is programmed to collect sensitive personal information like passwords, login credentials, contact details, and more. If you encounter any difficulties in removing the Support@freshingmail.top virus, please mention them in the comments, and we will provide assistance.
Step 1
Press CTRL, ALT, DEL keys together.
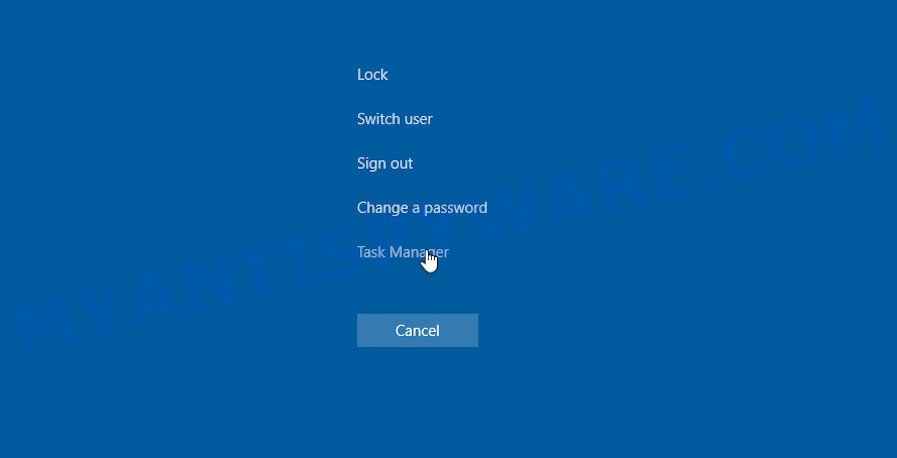
Click Task Manager. Select the “Processes” tab, look for something suspicious that is the Support@freshingmail.top ransomware then right-click it and select “End Task” or “End Process” option. If your Task Manager does not open or the Windows reports “Task manager has been disabled by your administrator”, then follow the guide: How to Fix Task manager has been disabled by your administrator.
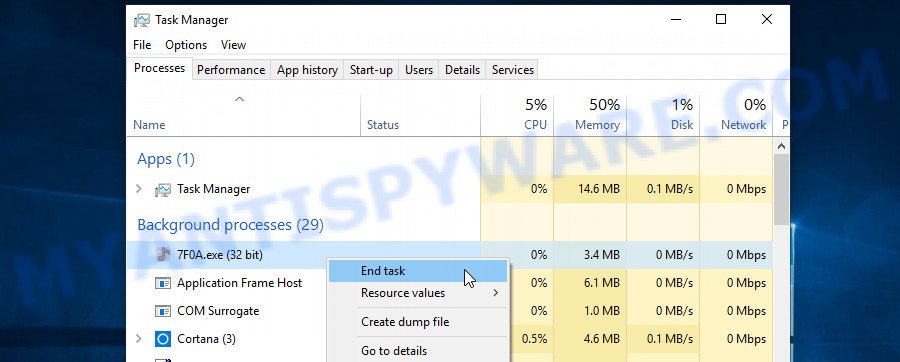
It is not difficult to detect a process related to the STOP ransomware. When looking for a malicious process, pay attention to the process icon and its name. Most often, this ransomware has a process name in the following format: 4-characters.tmp.exe or 4-characters.exe. For example: 7533.tmp.exe, A4b1.exe, CD15.tmp.exe, 19b2.exe. The process name can also contain “(32 bit)”. If you do not find a process with a similar name in the list of processes, then most likely the ransomware has finished working. But keep in mind, if you do not remove the ransomware autostart entries, as demonstrated below, and do not delete its file, then after a while it may start again, and if it finds unencrypted files, immediately encrypt them.
Step 2
Select the “Start-Up” tab, look for something similar to the one shown in the example below, right click to it and select Disable.
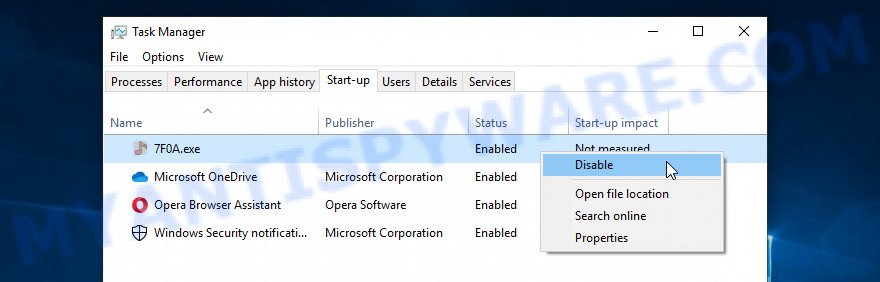
Close Task Manager.
Step 3
Type “Task Scheduler” in the search bar. Click Task Scheduler app in the search results. Click “Task Scheduler Library” in the left panel. On the right panel, right-click to “Time Trigger Task” and select Delete.
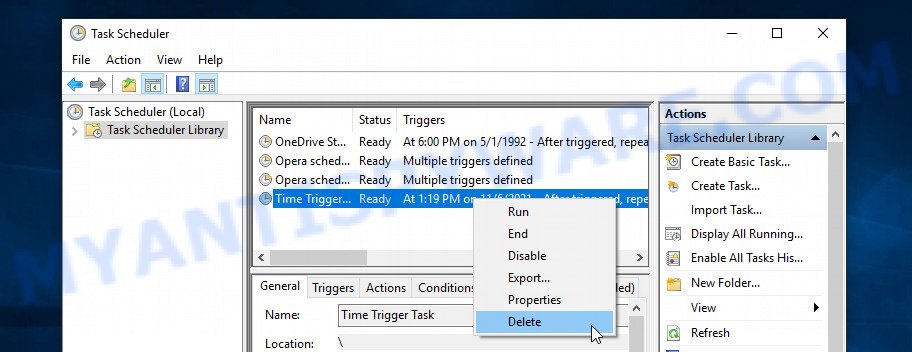
Close Task Scheduler.
Step 4
Run Task Manager and select the “Start-Up” tab. Right click to the ransomware Start-Up entry and select Open File Location as shown below.
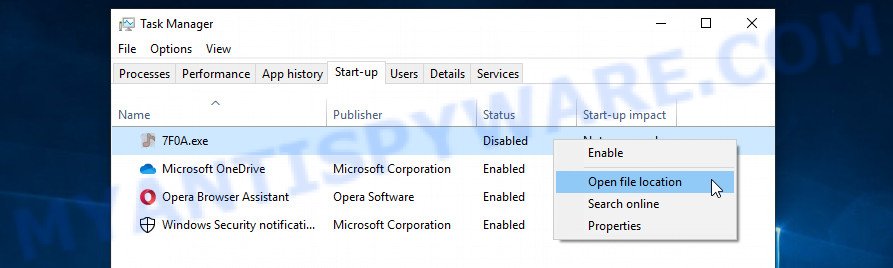
A directory containing one file will open in front of you, this file is the Support@freshingmail.top virus. It needs to be removed. If you try to delete it immediately, then you will not succeed, since this file is protected from deletion.
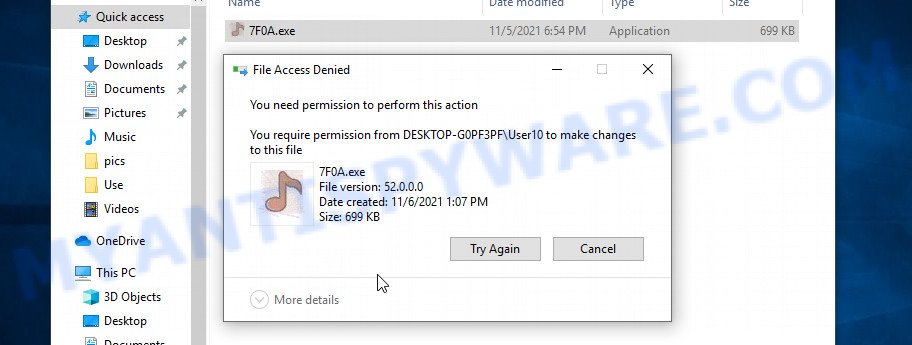
To delete this file, you need to do the following. Right-click on the file, select Properties. In the window that opens, select Security tab. Next, click the Advanced button below. A window will open as shown in the following example.
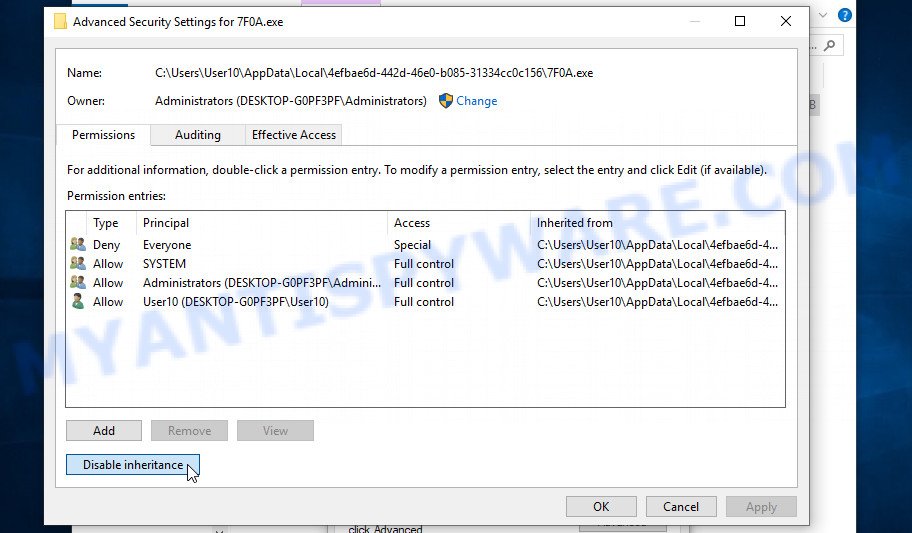
Click Disable inheritance. In the Block inheritance dialog box that opens, select the first item (Convert inherited permissions…) as shown below.
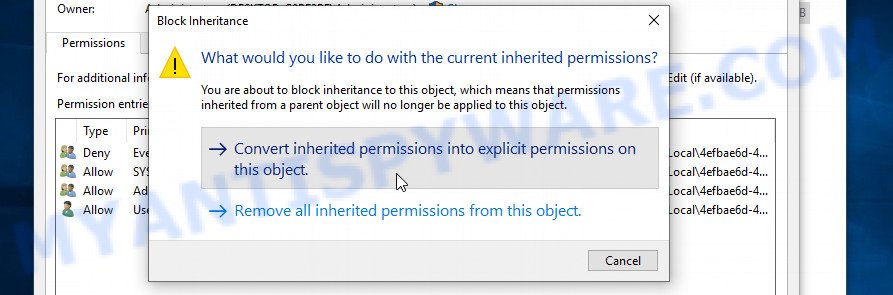
In the Permission entries list, select “Deny Everyone”, click Remove button and then OK. Close the file properties window. You should now be able to remove the ransomware. Right-click on the file and select Delete.
Scan computer for malware
MalwareBytes Anti-Malware (MBAM) is an antimalware program that can help you remove the Support@freshingmail.top ransomware. It can be used to remove almost all the forms of security threats such as ransomware, trojans, worms, adware, browser hijackers, potentially unwanted software and other malicious software. MalwareBytes has real-time protection that can defeat most malicious software and ransomware. Despite so many features, it does not reduce the performance of your computer. You can use MalwareBytes with any other antivirus without any conflicts.
First, please go to the link below, then click the ‘Download’ button in order to download the latest version of MalwareBytes AntiMalware.
327050 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
When the downloading process is done, close all windows on your computer. Further, launch the file named MBSetup. If the “User Account Control” dialog box pops up like below, click the “Yes” button.
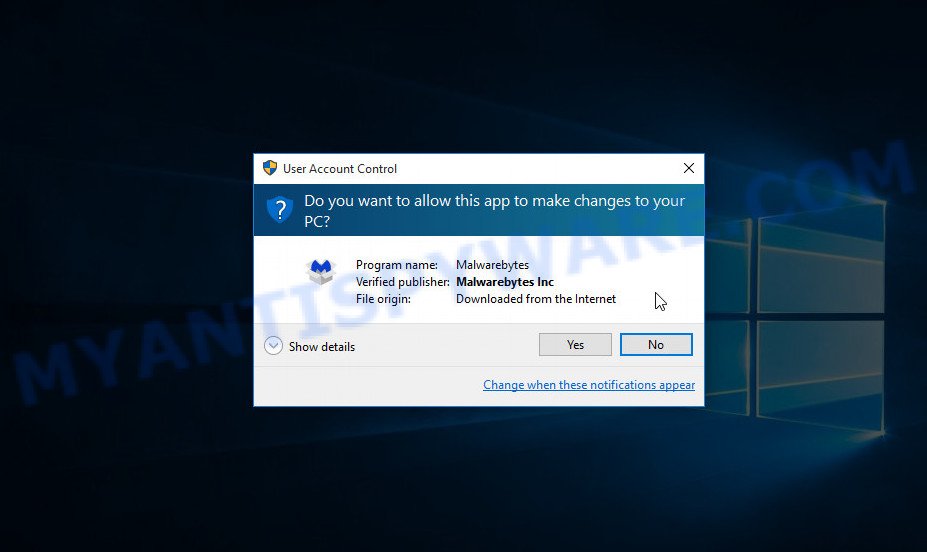
It will show the Setup wizard which will help you install MalwareBytes on the computer. Follow the prompts and do not make any changes to default settings.
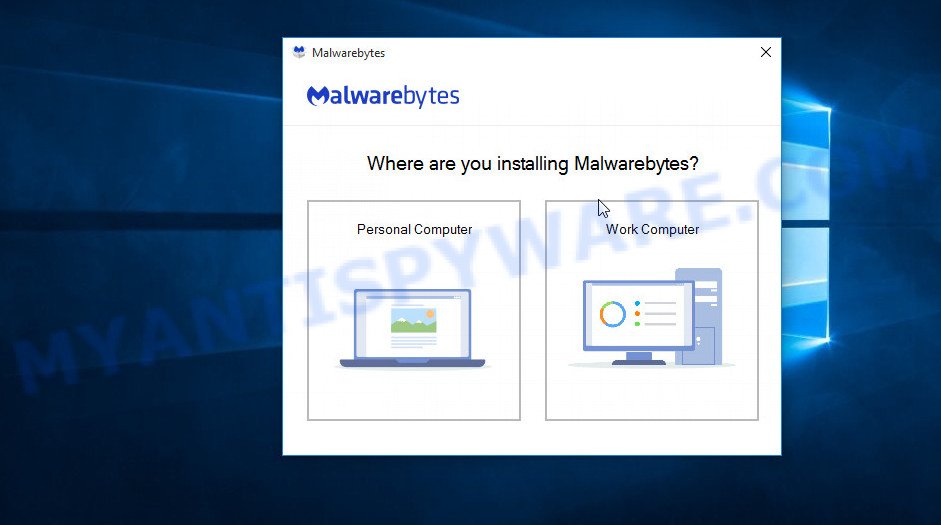
After the setup is complete successfully, press “Get Started” button. Then MalwareBytes AntiMalware will automatically run and you can see its main window such as the one below.
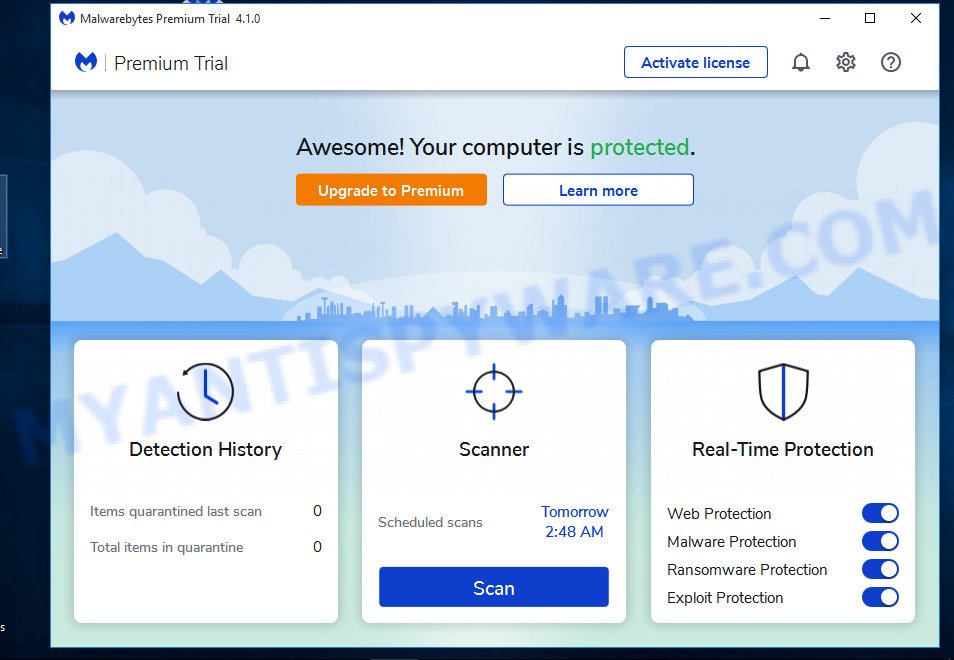
Next, click the “Scan” button for scanning your computer for the Support@freshingmail.top ransomware and other security threats. A system scan can take anywhere from 5 to 30 minutes, depending on your computer. While the MalwareBytes program is scanning, you can see how many objects it has identified as threat.
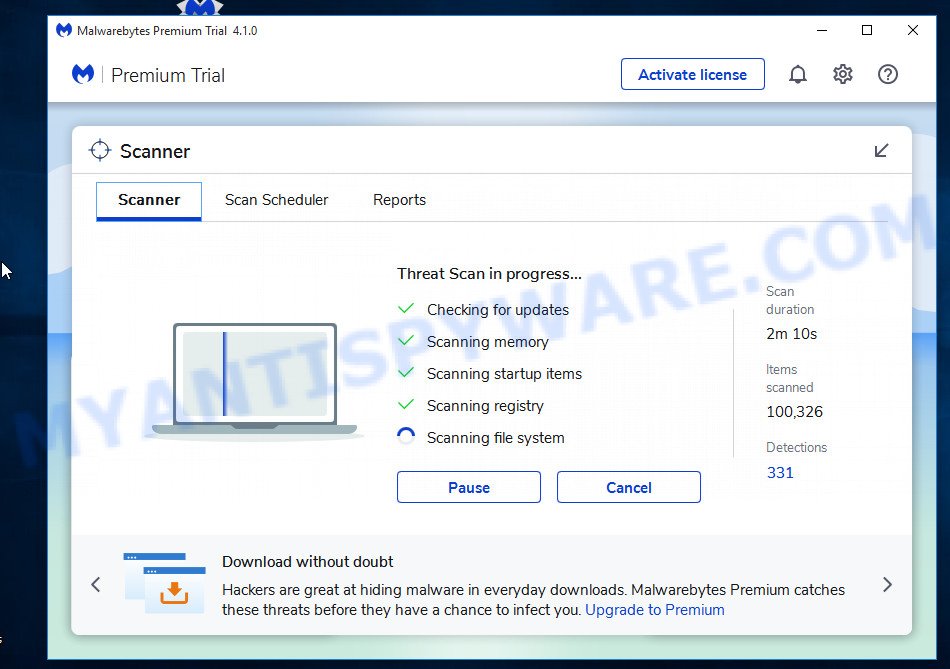
When the scanning is done, the results are displayed in the scan report. In order to remove all threats, simply press “Quarantine” button.
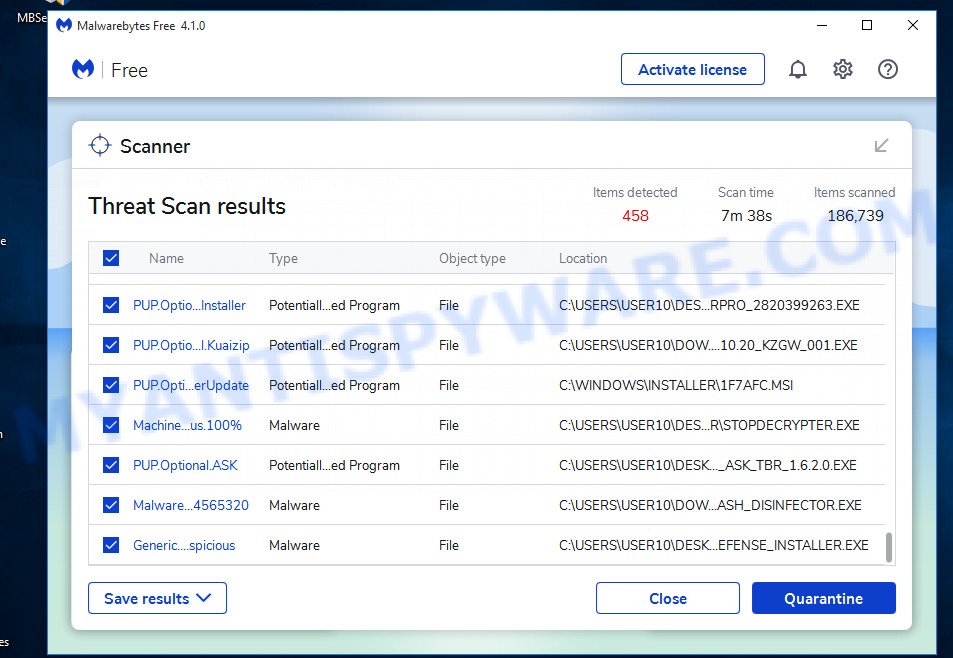
MalwareBytes Anti-Malware will remove the Support@freshingmail.top virus related folders,files and registry keys and move the selected threats to the program’s quarantine. Once that process is done, you can be prompted to reboot your computer.
In order to be 100% sure that the computer no longer has the Support@freshingmail.top virus, we recommend using the Kaspersky virus removal tool (KVRT). It is a free removal tool which can scan your PC for a wide range of security threats such as ransomware, adware, spyware, PUPs, trojans, worms as well as other malware. It will perform a deep scan of the computer including hard drives and Windows registry. After a malicious software is found, it will help you to remove all found threats from your computer by a simple click.
Download Kaspersky virus removal tool (KVRT) from the following link. Save it on your Windows desktop.
129229 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
Once downloading is complete, double-click on the Kaspersky virus removal tool icon. Once initialization process is finished, you’ll see the KVRT screen as shown in the figure below.
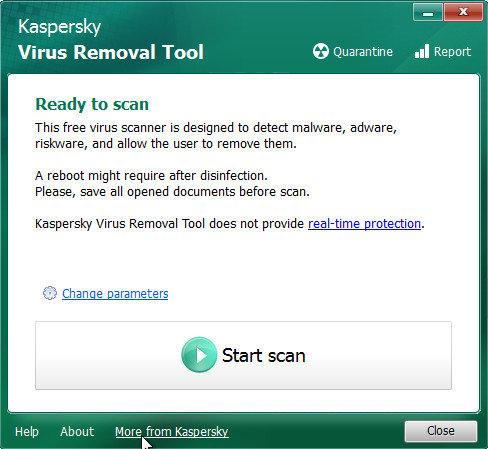
Click Change Parameters and set a check near all your drives. Click OK to close the Parameters window. Next click Start scan button . KVRT utility will start scanning the whole PC to find out the Support@freshingmail.top crypto virus . While the utility is scanning, you may see number of objects and files has already scanned.
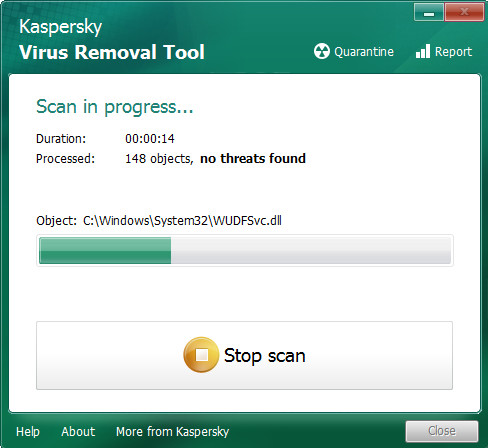
After the checking is finished, you can check all items detected on your personal computer as displayed below.
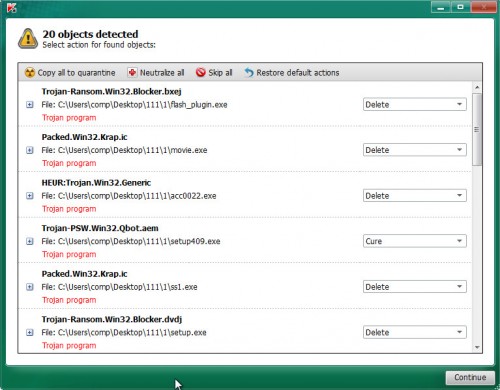
Review the report and then press on Continue to begin a cleaning procedure.
How to decrypt encrypted files
To decrypt encrypted files, you need to use a unique key and decryptor. Security researchers confirm that it is impossible to access the contents of encrypted files without decryption. Renaming the affected files, changing their extension cannot help the victim, the files will still remain encrypted. Fortunately, Emsisoft created a free decryptor, which in some cases can decrypt encrypted files.
Attention, be sure to scan your computer for ransomware before decrypting encrypted files. You must be 100% sure that there is no ransomware on the computer. To scan your computer for ransomware, we recommend using free malware removal tools.
STOP Djvu decryptor
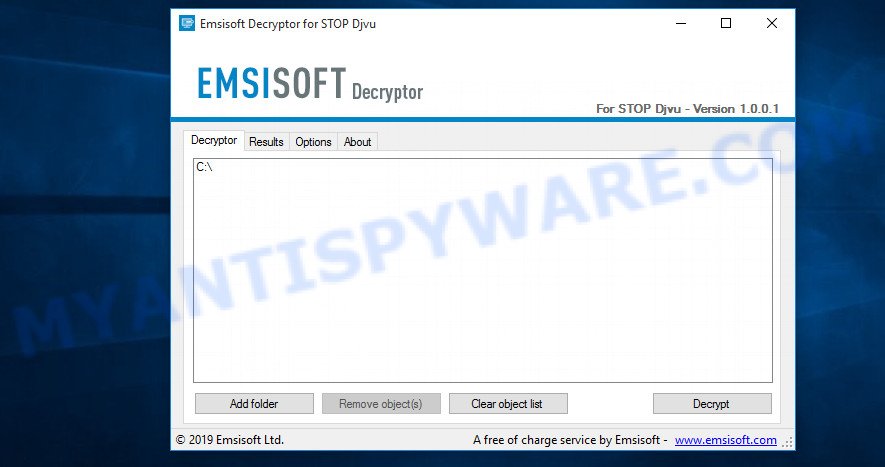
To decrypt encrypted files, use STOP Djvu decryptor
- Download STOP Djvu decryptor from the following link.
STOP Djvu decryptor - Scroll down to ‘New Djvu ransomware’ section.
- Click the download link and save the decrypt_STOPDjvu.exe file to your desktop.
- Run decrypt_STOPDjvu.exe, read the license terms and instructions.
- On the ‘Decryptor’ tab, using the ‘Add a folder’ button, add the directory or disk where the encrypted files are located.
- Click the ‘Decrypt’ button.
STOP Djvu decryptor is a free software that can decrypt the encrypted files only in some cases, when the files were encrypted with an ‘offline key’. If the files were encrypted with an ‘online key’, then they cannot be decrypted. The reason for this is that the decryption key is in the hands of criminals and this key can not be determined. But even in this case, there is a chance to restore the contents of encrypted files, we will talk about how to do this a little later.
How to find out which key was used to encrypt files
Below we show two ways to help you determine what type of key was used to encrypt your files. This is very important, since the type of key determines whether it is possible to decrypt encrypted files. We recommend using the second method, as it is more accurate.
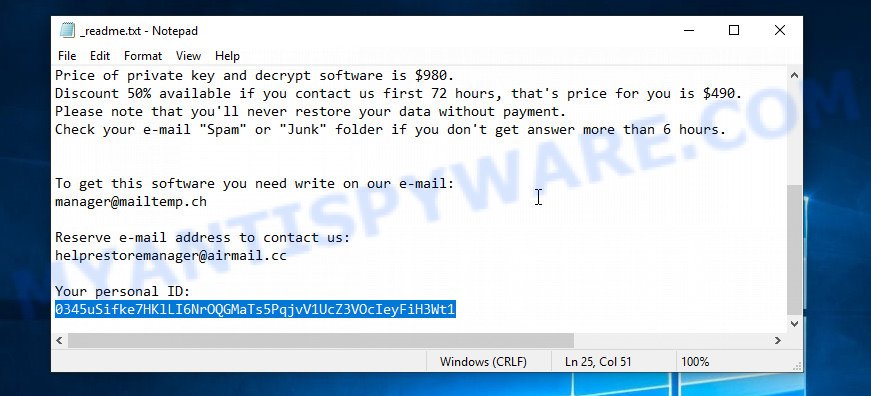
Personal ID is highlighted here
Find out the type of key using ‘_readme.txt’ file
- Open the ransom demand message (‘_readme.txt’ file).
- Scroll down to the end of the file.
- There you will see a line with the text ‘Your personal ID’.
- Below is a line of characters – this is your personal id.
Find out the type of key using ‘PersonalID.txt’ file
- Open disk C.
- Open directory ‘SystemID’.
- Open file named ‘PersonalID.txt’. This file lists ‘Personal ID’s that match the keys that the Support@freshingmail.top virus used to encrypt files.
The ‘Personal ID’ is not a key, it is an identifier related to a key that was used to encrypt files. If the ID ends with ‘t1’, then the files are encrypted with an offline key. If the ID does not end with ‘t1’, the ransomware used an online key. If you could not figure out how to determine which key was used to encrypt files, then we can help. Just write a request here or in the comments below.
STOP Djvu decryptor : “No key for New Variant online ID”
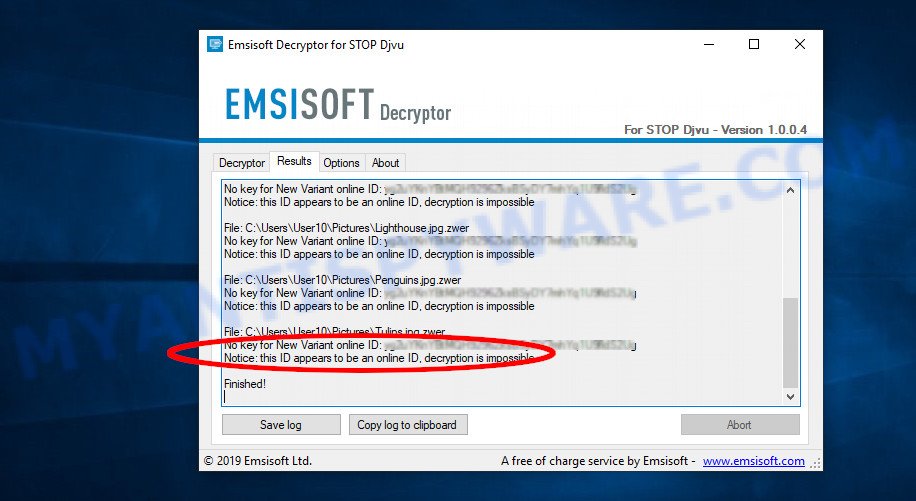
If, when you try to decrypt encrypted files, STOP Djvu decryptor reports:
No key for New Variant online ID: *
Notice: this ID appears to be an online ID, decryption is impossible
It means that your files are encrypted with an ‘online key’ and their decryption is impossible, since only the ransomware authors have the key necessary for decryption. In this case, you need to use alternative methods listed below to restore the contents of encrypted files.
STOP Djvu decryptor : “No key for New Variant offline ID”
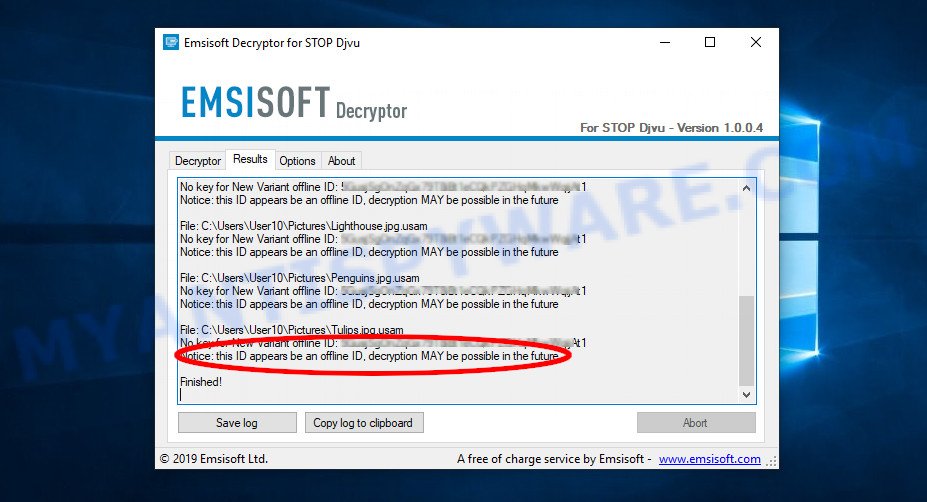
If, during decryption of encrypted files, STOP Djvu decryptor reports:
No key for New Variant offline ID: *t1
Notice: this ID appears be an offline ID, decryption MAY be possible in the future.
It means the following: your files are encrypted with an ‘offline key’, but the key itself has not yet been obtained by security researchers, in this case, you need to be patient and wait a while, in addition, you can also use alternative ways for recovering encrypted data.
If for some reason you were unable to decrypt the encrypted files, then We recommend to follow the news on our Facebook or YouTube channels. So you ‘ll know right away that it ‘s possible to decrypt ecnrypted files.
This video step-by-step guide will demonstrate How to use STOP Djvu decryptor to Decrypt encrypted files.
How to restore encrypted files
If STOP Djvu decryptor did not help you, or your files are encrypted using an online key, then there is no need to panic! There are several other alternative methods that may allow you to restore the contents of encrypted files. Once again, remember to be sure to scan your computer for ransomware and malware using free malware removal tools. You must be sure that the Support@freshingmail.top virus is completely removed.
Each of the methods presented below uses a different mechanism for recovering encrypted files. So try each one. It often happens that if the first method did not help, then the second helped.
Use shadow copies to recover encrypted files
First of all, try to recover encrypted files from Shadow Volume Copies, which are automatically created by Windows OS. In order to restore photos, documents and music encrypted by ransomware you can use a tool called ShadowExplorer. We recommend using this free utility because it is small in size, has a simple interface and does not require installation on a computer. Unfortunately, ransomware often removes all Shadow copies. Therefore, if Shadow Explorer cannot help you, then immediately proceed to the second method, which is given below.
Installing the ShadowExplorer is simple. First you’ll need to download ShadowExplorer on your MS Windows Desktop by clicking on the link below.
439443 downloads
Author: ShadowExplorer.com
Category: Security tools
Update: September 15, 2019
After the downloading process is done, open a directory in which you saved it. Right click to ShadowExplorer-0.9-portable and select Extract all. Follow the prompts. Next please open the ShadowExplorerPortable folder as displayed in the figure below.
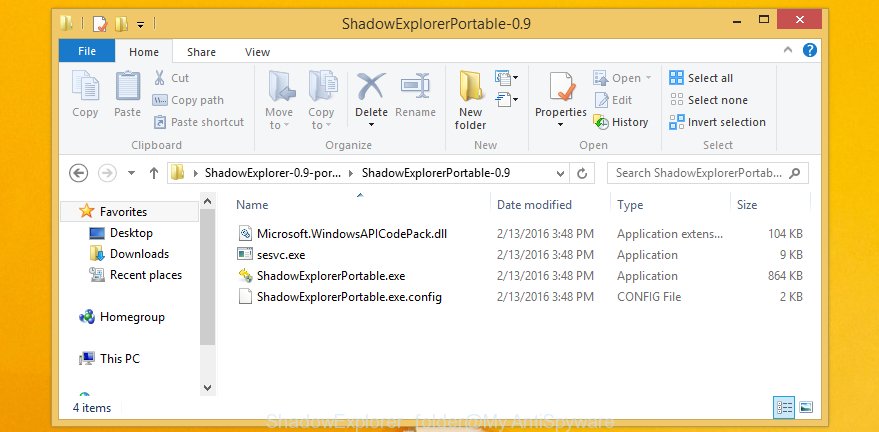
Double click ShadowExplorerPortable to start it. You will see the a window similar to the one below.
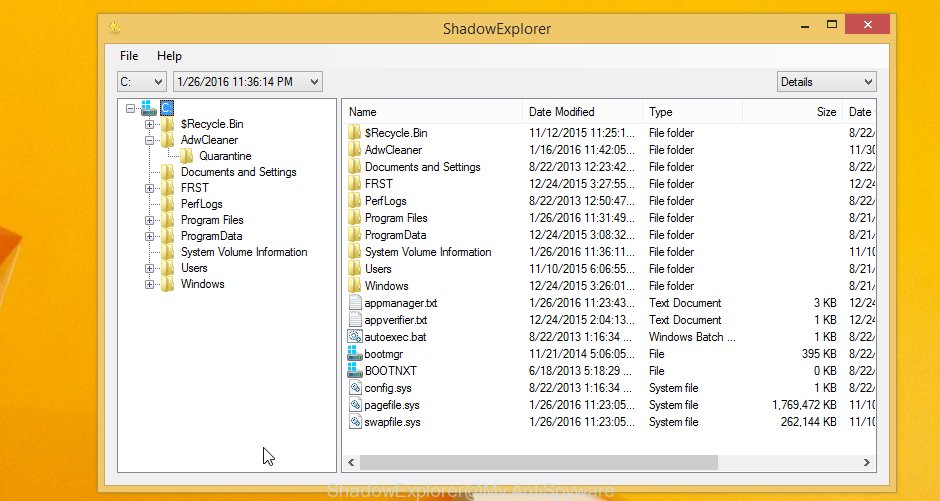
In top left corner, choose a Drive where encrypted documents, photos and music are stored and a latest restore point as displayed in the following example (1 – drive, 2 – restore point).
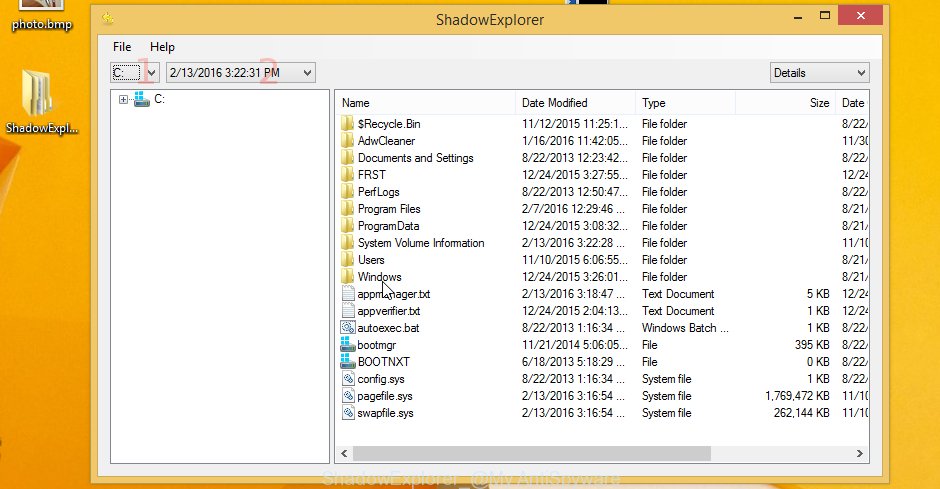
On right panel look for a file that you wish to restore, right click to it and select Export as shown in the figure below.

This video step-by-step guide will demonstrate How to recover encrypted files using Shadow Explorer.
Use PhotoRec to restore encrypted files
Another alternative way to recover encrypted files is to use data recovery software. This method requires a lot of time, but in most cases it allows you to recover part, and sometimes all, encrypted files. To restore encrypted files, use a free tool called Photo Rec. It has a simple interface and does not require installation.
Download PhotoRec on your personal computer from the following link.
Once the download is finished, open a directory in which you saved it. Right click to testdisk-7.0.win and choose Extract all. Follow the prompts. Next please open the testdisk-7.0 folder as displayed on the image below.

Double click on qphotorec_win to run PhotoRec for Windows. It’ll show a screen as shown below.
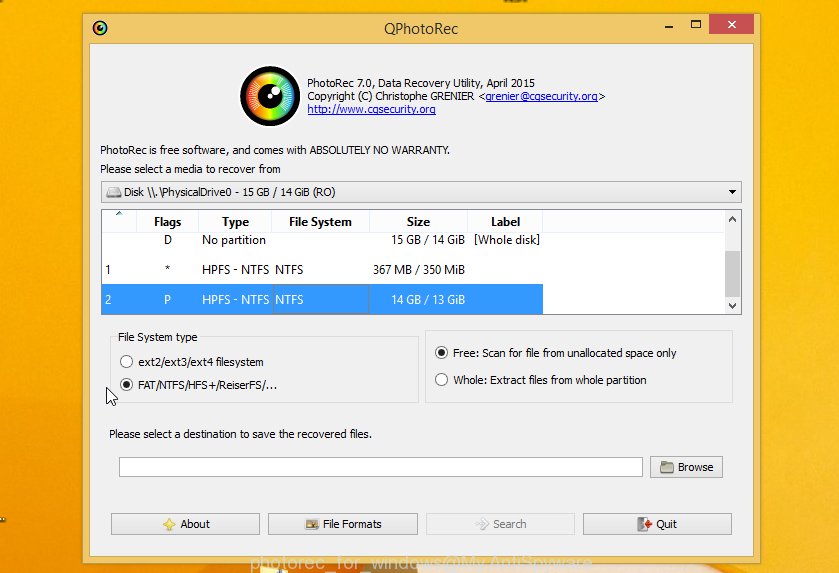
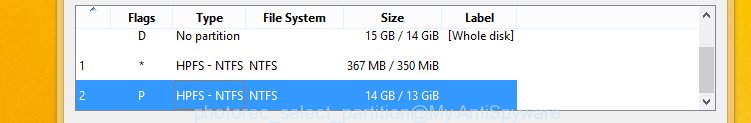
Choose a drive to recover as on the image below.
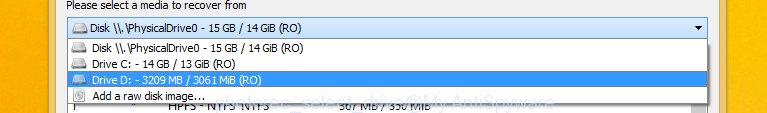
You will see a list of available partitions. Choose a partition that holds encrypted documents, photos and music as displayed in the figure below.
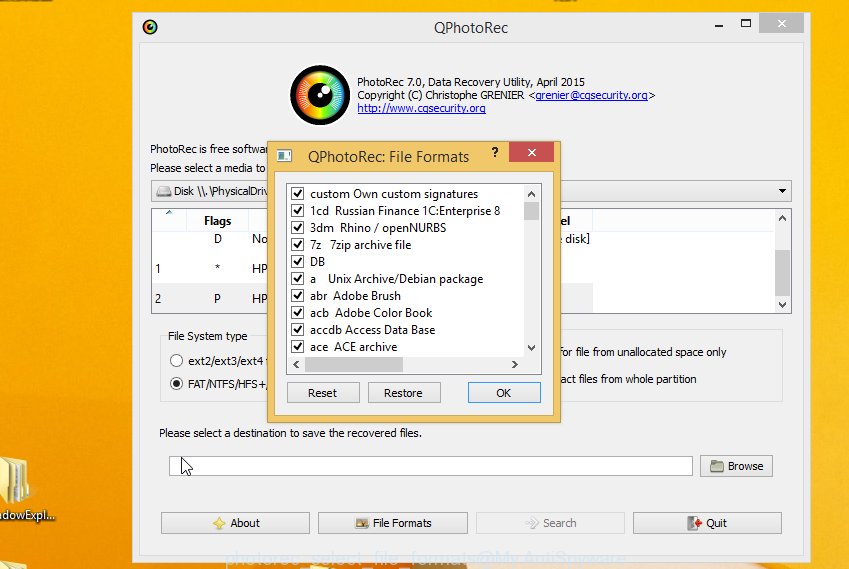
Press File Formats button and specify file types to recover. You can to enable or disable the recovery of certain file types. When this is done, press OK button.
Next, press Browse button to choose where restored personal files should be written, then click Search. We strongly recommend that you save the recovered files to an external drive.
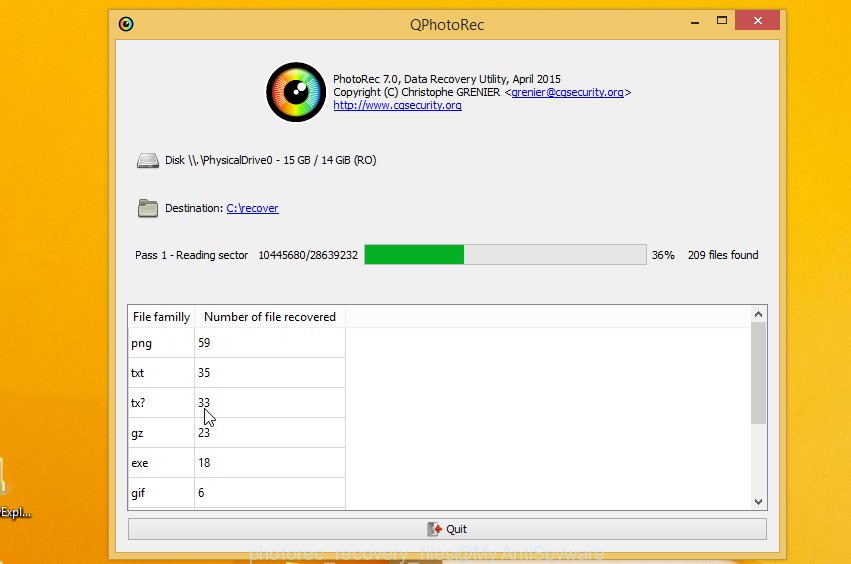
Count of restored files is updated in real time. All recovered personal files are written in a folder that you have chosen on the previous step. You can to access the files even if the recovery process is not finished.
When the recovery is done, click on Quit button. Next, open the directory where restored documents, photos and music are stored. You will see a contents as displayed in the figure below.
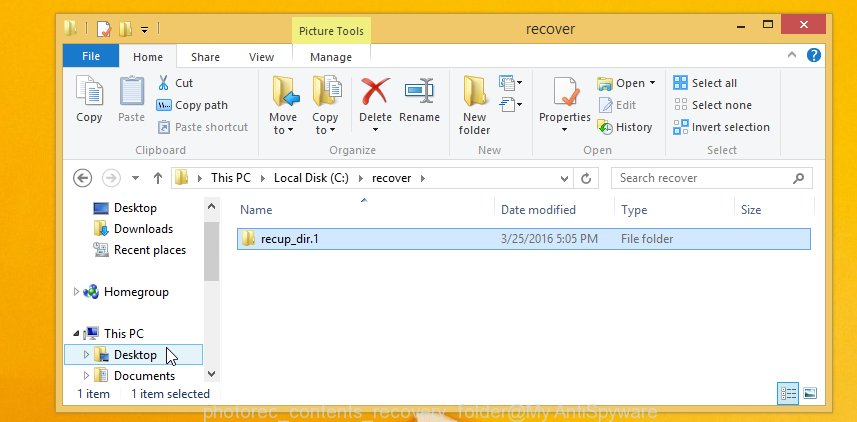
All restored documents, photos and music are written in recup_dir.1, recup_dir.2 … sub-directories. If you’re searching for a specific file, then you can to sort your recovered files by extension and/or date/time.
This video step-by-step guide will demonstrate How to recover encrypted files using PhotoRec.
How to protect your computer from ransomware
Most antivirus software already have built-in protection system against the ransomware. Therefore, if your computer does not have an antivirus application, make sure you install it. As an extra protection, use the HitmanPro.Alert. All-in-all, HitmanPro.Alert is a fantastic tool to protect your computer from any ransomware. If ransomware is detected, then HitmanPro.Alert automatically neutralizes malware and restores the encrypted files. HitmanPro.Alert is compatible with all versions of Microsoft Windows operating system from Windows XP to Windows 11.
Visit the following page to download HitmanPro.Alert. Save it directly to your Desktop.
When the downloading process is done, open the file location. You will see an icon like below.

Double click the HitmanPro.Alert desktop icon. Once the tool is launched, you will be displayed a window where you can choose a level of protection, as displayed in the following example.

Now click the Install button to activate the protection.
To sum up
This guide was created to help all victims of the Support@freshingmail.top ransomware. We tried to give answers to the following questions: how to remove ransomware; how to decrypt encrypted files; how to recover encrypted files; what is an online key and what is an offline key. We hope that the information presented in this manual has helped you.
If you have questions, then write to us, leaving a comment below. If you need more help with Support@freshingmail.top related issues, go to here.





















Muchas gracias por la informacion, lamentablemente mi clave de cifrado parece ser online… es la siguiente:
0844OSkwD4YDIPGvSAPEODaJn4YYzis8tYrorDWxRn5RxSy9
Saludos.
The “0844OSkwD4YDIPGvSAPEODaJn4YYzis8tYrorDWxRn5RxSy9” ID is related to an online key, so files cannot be decrypted. Try to restore the contents of encrypted files using the steps linked below: How to recover encrypted files.