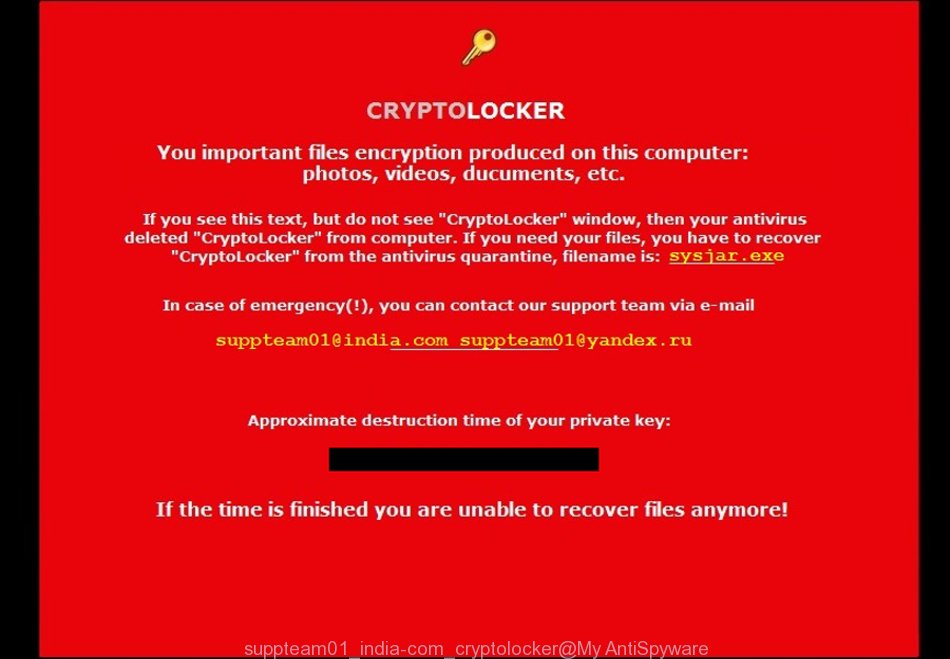
If your personal files, such as documents, photos, music does not open normally, you are seeing on the desktop a red ransom screen titled with “CryptoLocker” then your computer is infected with a new virus from a family of file-encrypting ransomware. Once started, it have encrypted your personal files stored on a computer drives and attached network drives.
It uses very strong hybrid encryption with a large key. Once the virus finished enciphering of all files, it will create a file named “Your files are locked !!!!.txt” with an instructions on how to decrypt all encrypted files.
The suppteam01@india.com virus offers to make a payment in Bitcoins to get a key to decrypt files. Important to know, currently not possible to decrypt files encrypted by the suppteam01@india.com ransomware without the private key and decrypt program.
If you choose to pay the ransom, there is no 100% guarantee that you can get back your files! If you do not want to pay for a decryption key, then you have a chance to restore your files. Use the step-by-step guide below to remove the virus itself and try to restore your files.
What is suppteam01@india.com ransomware?
Is my system infected with suppteam01@india.com ransomware?
How does my computer get infected with suppteam01@india.com virus ?
How to decrypt encrypted files ?
How to remove suppteam01@india.com virus?
How to restore encrypted files ?
How to prevent my computer from becoming infected by suppteam01@india.com ransomware?
What is suppteam01@india.com ransomware?
The suppteam01@india.com virus is a variant of ransomware infection from the CryptoLocker family. It affects all current versions of Windows operating systems such as Windows XP, Windows Vista, Windows 7, Windows 8, Windows 10. This virus uses the RSA-2048 encryption mode to eliminate the possibility of brute force a key, which will allow to decrypt all encrypted files.
When the virus infects a computer, it uses system directories to store own files. To run automatically whenever you turn on your computer, suppteam01@india.com ransomware creates a registry entry in Windows: sections HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ Run, HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ RunOnce, HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ Run, HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ RunOnce.
Immediately after the launch, the virus scans all available drives, including network and cloud storage, to determine which files will be encrypted. The ransomware uses the file name extension, as a way to define a group of files that will be subjected to encrypting. Encrypted almost all types of files, including common as:
0, .1, .1st, .2bp, .3dm, .3ds, .sql, .mp4, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mov, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm, .vcf, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .dba, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, wallet, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c, .p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt, .wav, .wbc, .wbd, .wbk, .wbm, .wbmp, .wbz, .wcf, .wdb, .wdp, .webdoc, .webp, .wgz, .wire, .wm, .wma, .wmd, .wmf, .wmv, .wn, .wot, .wp, .wp4, .wp5, .wp6, .wp7, .wpa, .wpb, .wpd, .wpe, .wpg, .wpl, .wps, .wpt, .wpw, .wri, .ws, .wsc, .wsd, .wsh, .x, .x3d, .x3f, .xar, .xbdoc, .xbplate, .xdb, .xdl, .xld, .xlgc, .xll, .xls, .xlsm, .xlsx, .xmind, .xml, .xmmap, .xpm, .xwp, .xx, .xy3, .xyp, .xyw, .y, .yal, .ybk, .yml, .ysp, .z, .z3d, .zabw, .zdb, .zdc, .zi, .zif, .zip, .zw
Once files are encrypted, the virus creates the txt-file named “Your files are locked !!!!.txt”. This file contains instructions on how to decrypt all encrypted files. An example of these instructions:
Support e-mail: suppteam01@india.com suppteam01@yandex.ru Your personal files encryption produced on this computer: photos, videos, documents, etc. Encryption was produced using a unique public key RSA-2048 generated for this computer. To decrypt files you need to obtain the private key. The single copy of the private key, which will allow to decrypt the files, located on a secret server on the Internet; the server will destroy the key after 120 hours. After that nobody and never will be able to restore files. To obtain the private key for this computer, you need pay 1.7 Bitcoin (~1084 USD) --------------------------------------------------------------------------------------------------- Your Bitcoin address: xxx You must send 1.7 Bitcoin to the specified address and report it to e-mail customer support. In the letter must specify your Bitcoin address to which the payment was made. --------------------------------------------------------------------------------------------------- The most convenient tool for buying Bitcoins in our opinion is the site: https://localbitcoins.com/ There you can buy Bitcoins in your country in any way you like, including electronic payment systems, credit and debit cards, money orders, and others. Instructions for purchasing Bitcoins on account localbitcoins.com read here: https://localbitcoin...to-buy-bitcoins Video tutorial detailing on buying Bitcoins using the site localbitcoins.com here: http://www.youtube.c...h?v=hroPcR-0zSI How to withdraw Bitcoins from account localbitcoins.com to our bitcoin wallet: https://localbitcoin...m/faq#howto_buy Also you can use to buy Bitcoins these sites: https://www.bitstamp.net/ - Big BTC exchanger https://www.coinbase.com/ - Other big BTC exchanger https://www.moneypakforbitcoins.us/ - Buy BTC via Green Dot MoneyPak https://btcdirect.eu/ - Best for Europe https://coincafe.com/ - Recommended for fast, many payment methods https://bittylicious.com/ - Good service for Europe and World https://www.247exchange.com/ - Other exchanger
The suppteam01@india.com ransomware actively uses scare tactics by giving the victim a brief description of the encryption algorithm and showing a threatening message on the desktop. It is trying to force the user of the infected computer, do not hesitate to pay a ransom, in an attempt to recover their files.
Is my system infected with suppteam01@india.com ransomware?
Identify that your computer is infected with suppteam01@india.com ransomware quite easily. If your personal files, such as documents, photos, music does not open normally, that is, for example, when you try to open a document, Word reports that it is an unknown file type, then it is likely that the document is encrypted, and your computer is infected. Of course, the presence on the desktop a ransom screen or threatening message is a sign of infection.
If you suspect that you have opened a email that infected with suppteam01@india.com ransomware, but you does not see any symptoms of the infection, then do not turn off or restart your computer. First turn off the Internet! Then follow the steps in this guide, see How to remove the suppteam01@india.com virus. Another option, shut down the computer, remove the hard drive and check it on another computer.
How does my computer get infected with suppteam01@india.com virus
The suppteam01@india.com virus is usually distributed through the use of spam emails. Below is an email that is infected with a virus like this ransomware.
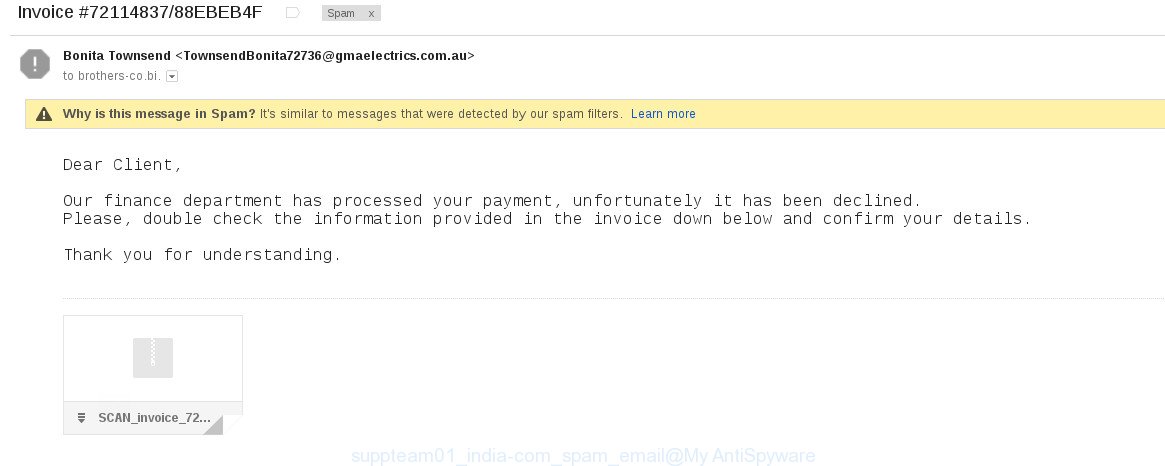
Once this attachment has been opened, this virus will be started automatically as you do not even notice that the suppteam01@india.com ransomware will start the encryption process. When this process is done, it will display the usual ransom instructions like above on the “Your files are locked !!!!.txt”.
How to decrypt encrypted files
Currently there is no available method to decrypt all files that encrypted by the suppteam01@india.com ransomware. The ransomware repeatedly tells the victim that uses a strong encryption algorithm with 2048-bit key. What does it mean to decrypt the files is impossible without the private key. Use a “brute forcing” method is also not a way because of the big length of the key. Therefore, unfortunately, the only payment to the authors of the suppteam01@india.com virus entire amount requested – the only way to try to get the decryption key.
There is absolutely no guarantee that after the payment of the authors of the suppteam01@india.com ransomware will provide the necessary key to decrypt your files. In addition, you must understand that paying money to the cyber criminals, you are encouraging them to create a new virus.
How to remove suppteam01@india.com virus
The following instructions will help you to remove suppteam01@india.com malicious software. Before doing it, you need to know that starting to remove the virus, you may block the ability to decrypt files by paying authors of the virus requested ransom.
Kaspersky Virus Removal Tool and Malwarebytes Anti-malware can detect different types of active ransomware and easily remove it from your computer, but they can not recover encrypted files.
Remove suppteam01@india.com virus with MalwareBytes Anti-malware
Download MalwareBytes Anti-malware (MBAM) from the link below.
MalwareBytes Anti-malware download link
Once downloaded, close all programs and windows on your computer. Open a directory in which you saved it. Double-click on the icon that named mbam-setup like below.

When the installation begins, you will see the Setup – Wizard that will help you install MalwareBytes Anti-malware on your computer.

Once installation is complete, you will see window similar to the one below.
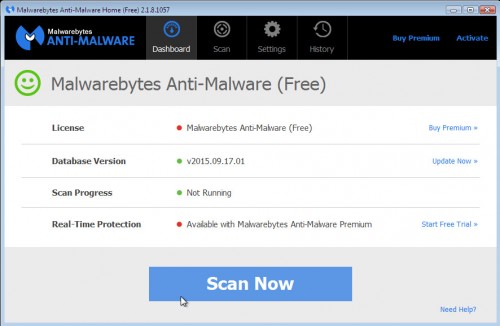
Now click on the Scan Now button to start scanning your computer. This procedure can take some time, so please be patient.

When the scan is finished, make sure all entries have “checkmark” and click Remove Selected button. MalwareBytes Anti-malware will start to remove ransoware related files, folders, registry keys. Once disinfection is completed, you may be prompted to Restart.
Remove suppteam01@india.com virus with Kaspersky virus removal tool
Download Kaspersky virus removal tool from here and save it directly to your Windows Desktop.
Double-click on the KVRT icon found on your desktop. Once initialization process is finished, you will see the Kaspersky virus removal tool screen as shown below.
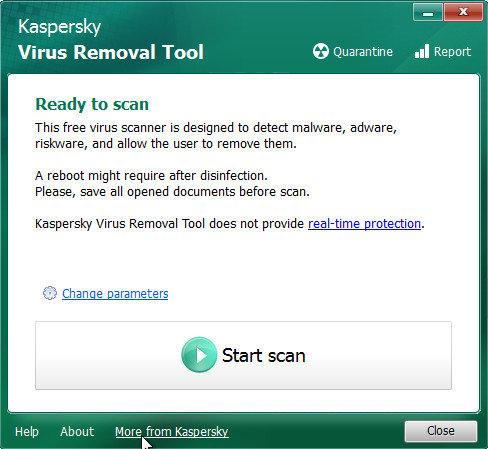
Click Change Parameters and set a check near all your drives. Click OK to close the Parameters window. Next click Start scan button. Kaspersky virus removal tool will now start scanning your computer for known infections. This procedure can take some time, so please be patient.
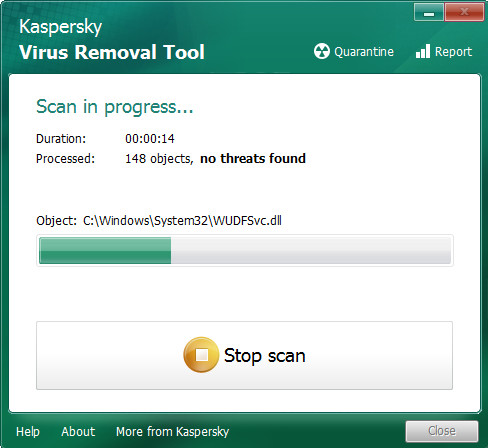
When KVRT has finished scanning, you will see a screen like shown below.
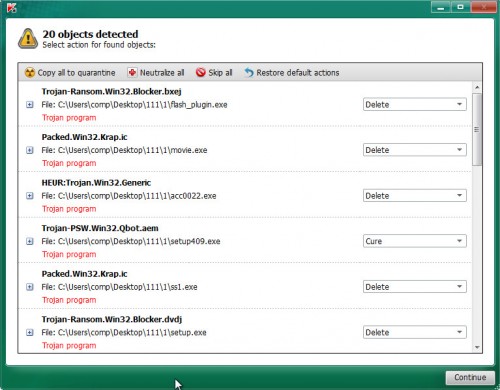
Click on Continue to start a cleaning process.
How to restore encrypted files
In some cases, you can recover files encrypted by the suppteam01@india.com ransomware. Try both methods. Important to understand that we cannot guarantee that you will be able to recover all encrypted documents, photos and other files.
Restore encrypted files with ShadowExplorer
Download ShadowExplorer from the following link.
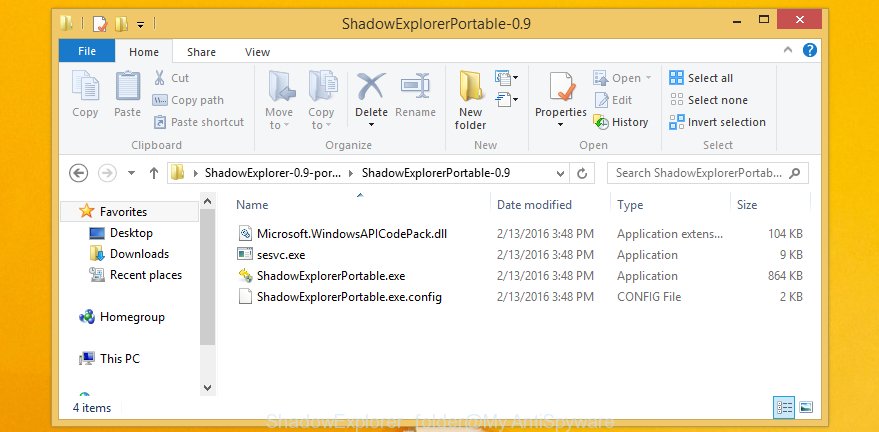
Open a directory in which you saved it. Right click to ShadowExplorer-0.9-portable and select Extract all. Follow the prompts. Next please open the ShadowExplorerPortable folder as shown below.
Double click ShadowExplorerPortable to run it. You will see the following screen.
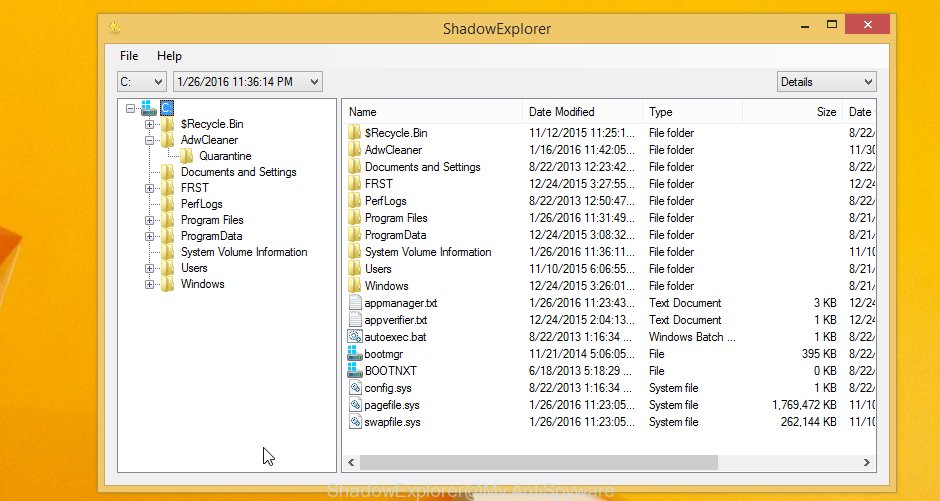
In top left corner, select a Drive and a latest restore point as shown on the example below (1 – drive, 2 – restore point).
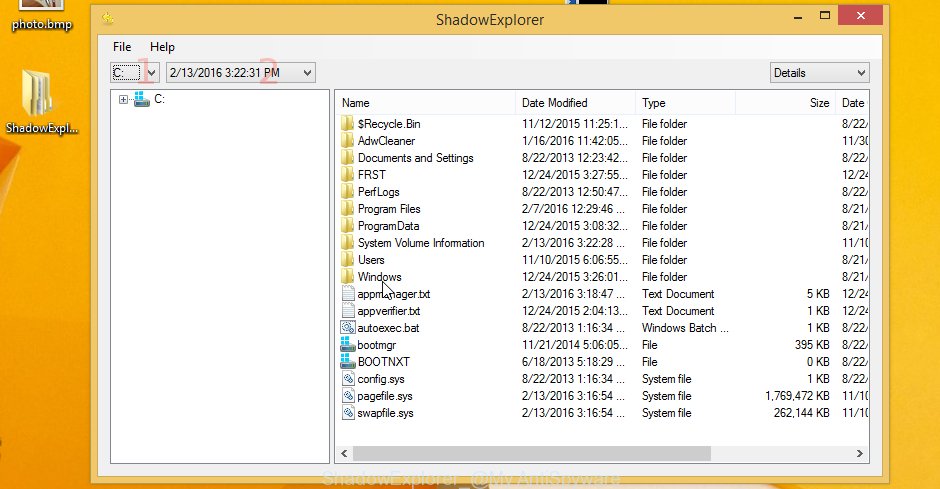
On right panel look for a file that you want to restore, right click to it and select Export. An example below.

Restore encrypted files with PhotoRec
Download PhotoRec from the link below.
Open a directory in which you saved it. Right click to testdisk-7.0.win and select Extract all. Follow the prompts. Next please open the testdisk-7.0 folder as shown below.

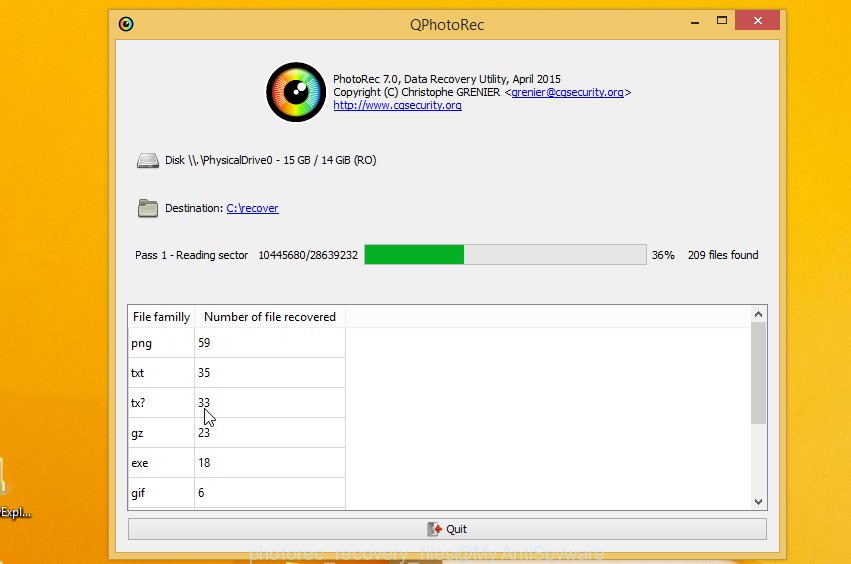
Double click on qphotorec_win to run PhotoRec for Windows. It will open a screen like below.
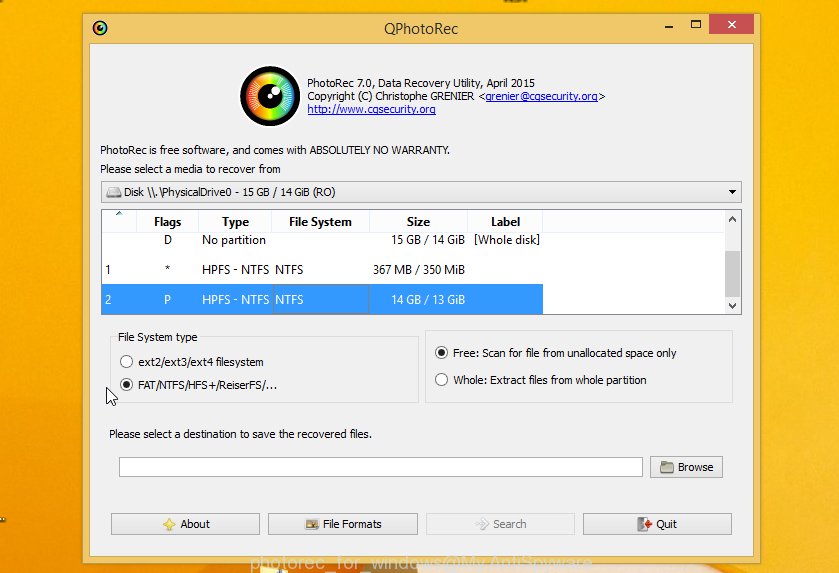
Select a drive to recover from as shown below.
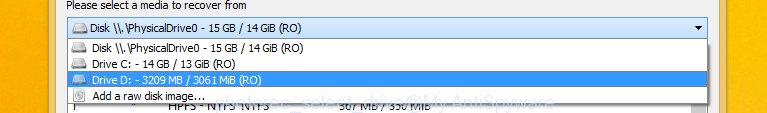
You will see a list of available partitions. Select a partition that holds the lost and encrypted files. An example below.
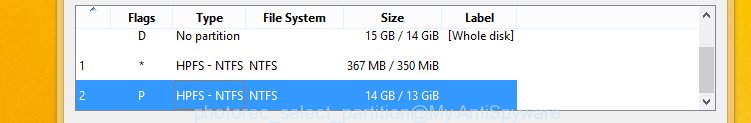
Click on File Formats button and select file types to recover. You can to enable or disable the recovery of certain file types. When this is done, click OK button.
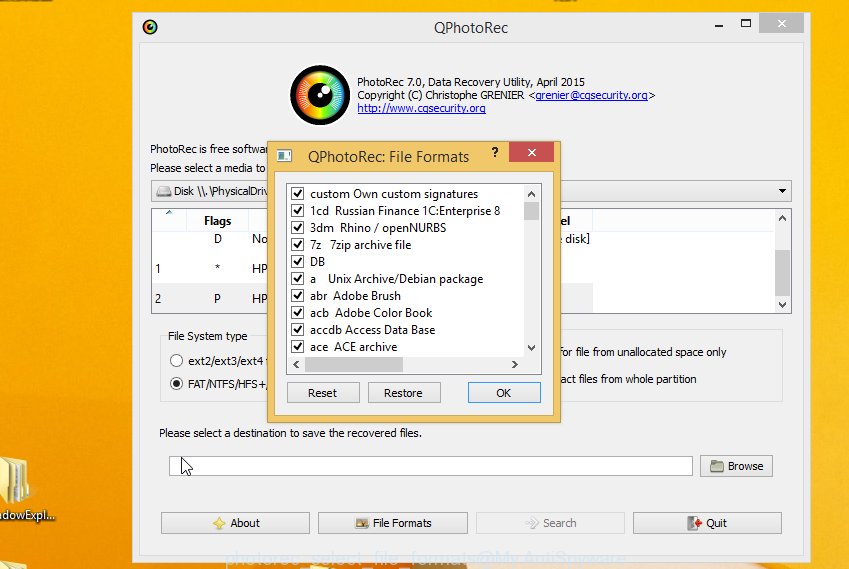
Next, click Browse button to select where recovered files should be written, then click Search.
Count of recovered files is updated in real time. All recovered files are written in a folder that you have selected on the previous step. You can to access the files even if the recovery process is not finished.
When the recovery is completed, click on Quit button. Next, open the directory where recovery files are stored. You will see a contents like below.
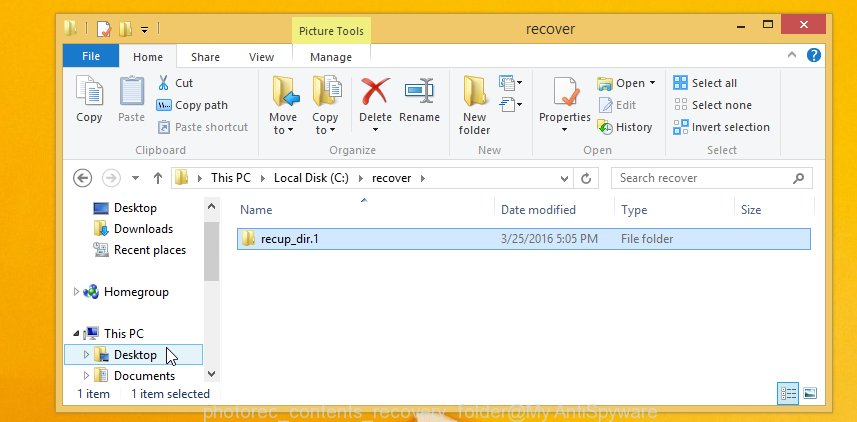
All recovered files are written in recup_dir.1, recup_dir.2 … sub-directories. If you are looking for a specific file, then you can to sort your recovered files by extension and/or date/time.
How to prevent my computer from becoming infected by suppteam01@india.com ransomware?
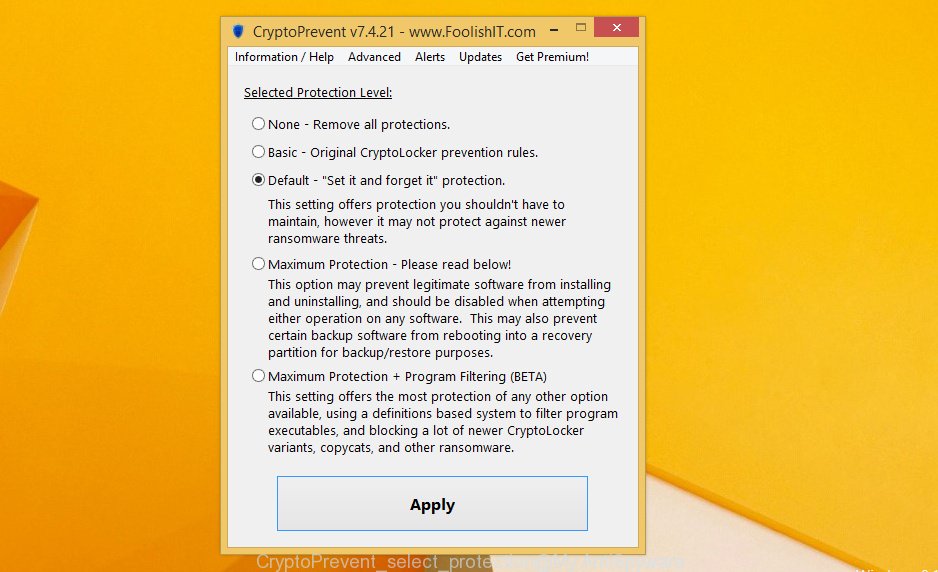
Most antivirus programs already have built-in protection system against the ransomware. Therefore, if your computer does not have an antivirus program, make sure you install it. As an extra protection, use the CryptoPrevent.
Download CryptoPrevent from the link below.
www.foolishit.com/download/cryptoprevent/
Run it and follow the setup wizard. Once the installation is completed, you will be shown a window where you can select a level of protection, as shown in the following example.
Click the Apply button to activate the protection.
The End.
Your computer should now be free of the suppteam01@india.com virus infection. If you need help with the instructions, then ask for help here.